
Our company offers, IT consulting services for customers seeking to interconnect their IoT and machine wireless devices to cloud or on-premise environment Network through the use of our customized FusionTrust connectivity service offering.
What is FusionTrust Connectivity offering?
- FusionTrust connectivity service offering is a way to connect your network securely.
- It’s a uniquely created service by our company DBA Binary Fusion, based on an industry recognized Zero Trust Connectivity architecture, categorized and dissected based on multiple consulting functions and responsibilities.
- Currently there are multiple vendors out there who provide Zero Trust Connectivity.
- Our company is vendor agnostic and therefore FusionTrust service offering is also vendor agnostic.
- We work with multiple types of Zero Trust Connectivity type of vendors. However our primary core vendor who we work with the most is Zscaler.
- As part of our FusionTrust service, Zscaler Zero Trust Connectivity plays an integral key role for connecting customer networks. However, if Zscaler is not a good solution for your specific use case then we can also work with other vendors as well, whomever is the most affordable and best for the customer.
- With FusionTrust service we can help companies connect machines to machines, machines to cloud as well as IoT to cloud.
Need Help? Nor sure where to start?
- Looking for help inter-connecting together your newly created IoT?
- Trying to figure out how to interconnect your IoT or M2M devices to the Amazon AWS IoT cloud?
- Do you have some front end servers in the Amazon hosted as virtual servers that provide front-end functionality to some customers on the internet that eventually connects with some back-end servers that store some data such as let’s say date that you are hoping to receive from your in vehicle in the field and in motion IoT industrial devices?
- Do you have a use case where your existing engineers put something together locally, but struggling to make heads and tails of how to connect it outside of the local premises?
- Do you have the need to interconnect your in motion vehicles to your servers in the Amazon cloud?
- Are you wondering what is the best way to do it?
- Are you asking your self-questions what is the cheapest way of doing this?
- Are you asking yourself questions about IT security associated with your IoT device when making it connected to the Amazon cloud?
- Are you asking yourself whether or not there are any other gotchas within your existing IoT device that may result in negative customer experience down the road?
- Are you attempting to make heads and tails for how exactly your IoT will connect to your data center or cloud in a secure way?
- Are you trying to figure out if there are any other factors involved, such as costs, vibrations resulted from having your IoT in Motion, unstable DC electricity that depends on your car battery that can cripple your device from operating efficiently?
- Do you have a team of guys who are mostly focused on creating IoT product and thinking about the actual device itself vs thinking about how this device will actually connect to the network?
- Do you have the team of mechanics or extremely technical gurus who are only focused on doing specific tasks such as cooking up tactics to measure pressure, temperature or water levels or something else sensor related and gathering data locally, without really understanding how to send that data outside of your local IoT device?
- Do you have the need for making sure that the data gathered your devices such as temperature, or GPS coordinates, or speed or velocity or pressure gets properly transmitted from the moving vehicles to the cloud for your customers to see this data?
- Do you want to somehow track your employees using your IoT or track something else?
- Perhaps you want to track when and when employees started using the device, perhaps you want to know where your employees drove the vehicle to, perhaps you want to measure the pressure of a pump or of an air conditioner from the outside.
- Or perhaps you simply want consulting advice that can show you how to ensure that your existing IoT or M2M devices are properly communicating and not only communicating but communicating in a secure way yet at the same time at affordable cost or at least much more competitive than the market has to offer whatever the case maybe DBA Binary Fusion has got you covered.
-
Or perhaps you are thinking that you want to sell your IoT product on Amazon, but did you know that if your products get hacked you can get banned from Amazon completely, having solid double checking on your product and consulting advice from DBA Binary Fusion can help you out significantly from getting dropped out of market even before you get your product fully to the market.
No matter what your IoT or M2M connectivity use case is. Our Company DBA Binary Fusion helps start-ups, small and medium and large size companies interconnect their in-vehicle IoT to the cloud securely.
IoT and M2M Consulting for Mobile Connectivity

FusionTrust solution for IoT Mobile Connectivity. The solution that can help your existing IoT devices get connected to the cloud, regardless how they connect, wireless cellular way or through WIFI . Regardless what type of use case you have, machine 2 machine, IoT to cloud or remote work employees to the cloud.
Zero Trust Connectivity Consulting
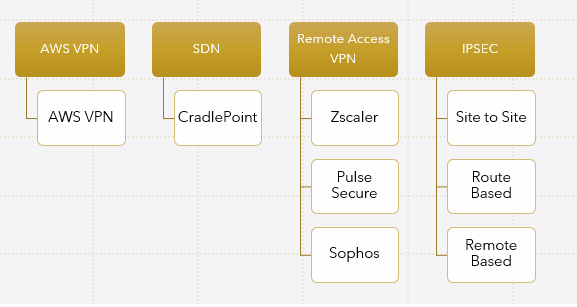
- Our company works with different types of vendors, ranging from Sophos, Fortigate, Checkpoint, Cisco, Ubiquiti, including Zscaler and many other vendors helping customers interconnect their branch offices, IoT devices to AWS or Azure, GCP clouds.
- We can help your IoT devices transition from your existing legacy VPN connectivity to Zero Trust Connectivity Model, making it possible for your IoT network be more secure.
- Additionally we can help you perform proof of concept for any other Zero Trust Connectivity specialized vendor that maybe cheaper or more suitable for your budget.
What type of FusionTrust IoT for Mobile connectivity solutions does our company offer?
- Our company can help you transition away from your existing VPN Solution provider into more secure Zero Trust Connectivity type of solution called FusionTrust for your existing offices, employees, IoT, Machine 2 Machines.
- We can also help companies configure multiple VPN providers for their IoT connectivity needs, where for example Zscaler is a primary method of connectivity while another Zero Trust Connectivity vendor is the secondary.
- We can engineer entire architecture for how to interconnect your IoT devices to the cloud using resilient architecture based on Zero Trust connectivity framework.
- Every engagement begins with IoT Network Connectivity Assessment
- Followed by proof of concept, execution and optional FusionCare IT managed services monitoring and support.
- After FusionTrust service is executed, FusionCare service follows, where our company continues to takes care of your network, helping your company maintain it, monitor it and support it.
Review your IoT Wireless Network
Create Project Plan
Create POC
Project Execution
FusionCare - IT Support
How Can We leverage Zscaler for IoT connectivity
ZPA -Zscaler Private access is sort of like Site To Site Tunneling type of solution with connectivity to your existing on premise offices and cloud based devices/applications.
Our company can help organizations interconnect their cloud based EC2 instances for example or containerized Kubernetes applications get easily interconnected with remote access users, cloud applications, on premise offices and users and IoT types of devices.
With ZIA Zscaler Internet Access solution our company can help customers integrate their existing offices with SaaS based Proxy solution, helping your employees be protected from malicious threats present in every day web. Visiting inappropriate sites should not be allowed in your company’s environment. It presents risks. Our company can help your company mitigate these risks, by integrating Zscaler ZIA Internet Security Solutions with your existing employee Windows or Macintosh laptops, reducing the chances for employees visiting sites and downloading malicious content.
Monitoring solutions are lacking behind when it comes to monitoring health of remote access connectivity. With ZDX (Zscaler Digital Experience) solution integration, our company can help your internal IT Staff be properly configured for remote access user monitoring, placing your internal IT Staff in the driver sit of being able to see who is having connectivity issues and where.
Industries we service:
- Manufacturing
- Professional LLCs
- Restaurants
- Construction
- Law
Monitoring web transaction logs and who visits what site is not exactly fun in Zscaler. Zscaler only keeps data for 6 months. Some customers prefer to offload it to Sumo Logic, for easier troubleshooting. Our company can help your company’s Zscaler environment get integrated with Sumo Logic, offloading advanced firewall logs, and web transaction logs into Sumo Logic from Zscaler.
How Can we leverage Cradlepoint for IoT connectivity?
- Cradlepoint has a very good offering of routers that can be leveraged with multiple SIM cards thanks to multiple modem hardware architecture, helping your IoT devices stay more resilient, offering multi cellular carrier connectivity with failback to wireless and wired method of connectivity.
- Cradelpoint integrates with Zscaler, and can be connected to Zscaler network.
- The complexity beyond doing so may vary depending on how savvy your IT Staff is.
- If your IT staff is not too savvy, and you need consultation advice to see how to make this integration happen or happen to be looking for end to end solution helping your IoT devices stay connected, then we can make this happen also.
Major Use Cases that are driving the need for our services.
Azure SAML and SCIM provisioning Integration with Zscaler
- Many customers out there simply stuck with so many service providers on the internet ranging from different carriers offering all sorts of wireless networks for mobile to mobile type of inter-connectivity to hardware and solution vendors who have variety tons of features on their integrated modem/router devices, that it’s really becoming extremely difficult to decide which solution makes the most sense, especially when other factors come into play such as the need for customers to interconnect to AWS IoT or other cloud providers.
- Major Drivers that fuel our customer’s needs. We realize that our customers also have customers, and also have responsibilities.
- That means our customers must know associated costs and other information that pertains to the wireless solution design for IoT, SDN, M2M in Vehicle Networks. Which is why we specialize in addressing these needs as one of our areas of focus and specialization.
So what are the most common needs and drivers of our customers?
- The need for wireless connectivity in moving devices.
- The need for digital signature such as contract signing in moving vehicles
- The need for measuring probe sensor or other types of sensors data in real time.
- The need for measuring speed, temperature, pressures or other statistical information that can help our customers have competitive IoT product.
- The need for being able to interconnect their existing physical data center or warehouse with the existing MPLS circuit to the mobile in-vehicle wireless networks.
- The need for being able to rely on wireless in vehicle and in motion wireless networking for passing internet traffic to the passengers within the vehicle
- The need for being able to track employees and anything that has anything in relationship to what these employees are doing on the job (whether it’s foam spraying, driving the truck, scanning signature of customers inside the vehicle, or providing possibility for customers to make payments or browse the internet all across different secure channels.
- The need for integrating cloud services into the mobile workforce in a way that helps a customer of customers manager in-vehicle networks.
- The need for having the flexibility of being able to control the field devices more easily and extend support to customer’s customers.
Challenges with IoT mobile connectivity
- How to secure IoT and M2M networks, and reduce hacking risk.
- How to make sure that IoT or M2M devices do not use too much data.
- How to view the usage and utilization of data
- How to gain visibility and resiliency
- How to upgrade the firmware of communication devices to avoid security breach issues in a way that doesn’t maximize on-site in the field costs.
- How to bridge connectivity between Wifi and Cellular devices and reduce the usage of wireless networks data to save money in the areas where connectivity is possible through wifi.
- How to bridge the gap between wired and wireless networks, meaning in certain cases, when the devices is on the customer premises and wifi is available there is no need to use precious 4g, 3g or 5g data, and flexibility to rely on wifi can be most certainly the best breed of both worlds.
- How to chose carriers who can help get connected.
- How to chose information technology components that can help wifi and wired in the field networks connect to the cloud.
- This hybrid approach creates variety methods of flexible and secure communications, that many solution companies talk about, yet none of them provide an exact picture of how exactly does all of that technology factor into customer’s overall solution.
- Tons and tons of companies in all over the place popping up proclaiming that they are experts in IoT, M2M and beyond. Yet many simply fail to understand exactly what customer’s needs are and only go half a mile vs going the full mile and providing quality service.
- With FusionCare we go the full mile, helping customers take control of their network.
With so Many Vendors out there many companies lose focus
Why so many solution companies who offer IT consulting services disconnected from many of their customers?
- Meaning, in some cases companies attempt to offer customers solutions that favorable mostly to the solution providers rather than favorable for the customer! In fact, that trend is very common, which is why the new profession and the new skill and the new trade has evolved, the trade of an IT Generalist type of professionals who can internetwork multiple mindsets, review dependencies and calculate the best type of solution that is appropriate to the customer.
- Other company on the other hand treats customer as the priority.
- DBA Binary Fusion is the IT Generalist (in fact we teach thousands of engineers how to become IT Generalist) and is the Network Consulting company who can help customers make the right decision when it comes to choosing the right type of in-vehicle and in motion wireless network design and solution while simply being neutral type of solution provider who is not locked down to a particular vendor or carrier, helping customers make the right decision in customer’s best interest sort of like the lawyers who are attempting to help clients.
FustionTrust Zscaler Tunneling Solutions and Services that we offer
- Our company offers the following FusionTrust IoT Mobile Connectivity services for small, medium, or large size companies, spread across multiple levels of teams and responsibilities.
- Depending on the customer we work with, FusionTrust connectivity partner maybe different.
- For example for some customers we pick Zscaler Connectivity partner to work with, for others Pulse Secure. In some cases we pick multiple partners for the purposes of redundancy.
IoT Operations and Support (FusionCare)
From start to finish maintenance and support
- We support your IoT devices
- Enroll connectivity of your devices to cloud network.
- Provision agents onto IoT devices.
- Upgrade/Update versions of IoT device connectivity agents.
- Resolving connectivity issues.
- Engaging FusionTrust connectivity vendor or resolution and support.
- Troubleshooting with cellular carriers and ISP connectivity issues.
Desktop Engineering
Initial and ongoing desktop/client support..
- Rolling out FusionTrust connectivity partner clients on MAC and Windows Laptops and other types of machines.
- Packaging FusionTrust agents and testing.
- Troubleshooting desktop-related compatibility issues between complex apps like Fiddler that don’t work well with FusionTrust connectivity partner or any other custom library types of developing apps or utilities that are having issues with FusionTrust connectivity partner.
- Installing root certificates from FusionTrust connectivity partner for custom-based apps.
- Troubleshooting blue screens of death types of issues or other connectivity-related issues due to agents incompatibility.
- Troubleshooting certificates with FusionTrust connectivity partner.
Enterprise Monitoring
Initial and ongoing monitoring.
- FusionTrust partner Connector Health Monitoring for CPU, Memory, connector health status, and beyond.
- Application Health Monitoring.
- Health Monitoring of User connections.
- Web Log & Advanced Firewall Monitoring.
- FusionSmart – Monitoring Zscaler logs & metrics in customer’s SIEM such as SumoLogic, Splunk, or DataDog or any other tool such as FusionView.
- Integration services with ServiceNow through SumoLogic or FusionView.
- Custom Dashboard Creation for FusionTrust connectivity partner infrastructure factors that make connectivity work, ranging from, Authentication, authorization, or any other type of KPIs, side by side with business transaction monitoring.
- Custom Alerts creation based on advanced outliers, logs/metrics.
- Monitoring Agents Instrumentation for servers, and other types of devices.
- FusionAuto: Automation of FusionTrust connectivity partner API-driven scripts for infrastructure health monitoring.
- FusionML: Machine Learning model building and creation of advanced monitoring and forecasting.
- FusionView: Custom API integration for monitoring outside of FusionTrust connectivity partner health dashboard view in a single FusionView unified portal, intermixed with other application health monitoring, including business transaction monitoring through the use of distributed tracing, metrics, and logs.
Professional Services (Network & Security Engineering)
First-time setup and continuous support.
- Troubleshooting connectivity with advanced types of applications that may not be compatible with your IoT devices or FusionTrust connectivity and creating workarounds and permanent solutions.
- Integration connectivity services with AWS, Azure, and IDPs for your IoT devices.
- Single Sign-On Integration for FusionTrust connectivity partner using SAML and SCIM.
- Source Anchor Forwarding Configuration and integration for greater interoperability.
- Advanced Firewall Configuration.
- FusionTrust connectivity partner integration with customer SIEM such as QRadar, Sumo Logic or Splunk Integration for web logging or advanced firewall logging.
- Isolated DMZ configuration and integration with on-prem environment for apps that are vulnerable, that require isolation.
- Custom creation of special policies to suit different types of connectivity needs and different types of operational workflows.
- Procedure creation for customer’s internal IT staff, the Infrastructure Operations team and the company’s employees.
- Advanced networking configuration for collaboration applications such as Teams, Zoom, AWS Workspaces, Azure AVD, etc, and others.
- The naming convention maintenance for all of your IoT devices and any associated connectivity dependencies.
Educational & Knowledge Transfer
First time and continuous driven effort.
- Educational Playbook Generation for company employees ranging from regular users, IT staff, and beyond.
- Creation of procedures in confluence/SharePoint for applications that are not proxy friendly.
- Internal enterprise engineering training for how to troubleshoot Zsclaer related issues.
Professional IT Consulting
For Small Large & Medium Size Businesses
FusionTrust IoT mobile connectivity customized service based on your existing environment
How we can help
FusionTrust
Packaged Service for companies seeking to maximize their security.
Read MoreFusionTrust - Zero Trust Connectivity Services
Here are the services that we offer for Zero Trust Connectivity customers.
- Design of your entire Zero Trust Network
- Identify existing applications and their DNS associated names.
- Implement connector connectivity.
- Create naming hierarchy for your IoT devices and for FusionTrust connectivity partner connectors.
- Interconnect multiple VPCs in your AWS environment together your IoT mobile cellular network.
- Ensure that your existing applications that conduct patching of your systems work with FusionTrust by leveraging our FusionScan and FusionPatch service.
- Create customized source anchor forwarding policy exceptions for applications that don’t behave well with different public IP addresses.
- Permission management.
- Cloudwatch configuration for metrics and logs.
- Transit Gateway VPN configuration.
- Virtual Private Gateway setup for small and medium offices.
- Certificate ACM building, helping you create certificate authority and making certificate based authentication work.
Cost Analysis & Savings
When many of our customers reach out to us, rarely does every customer know all the associated costs with the solution, simply because there are many factors associated with building VPN tunnels and making them work with the cloud, or creating Zero Trust Connectivity fortified network.
As part of our FusionTrust solution offering, we help customers pick the most optimal cost-effective options for their connectivity needs, and part of the engagement conduct Network Assessment, making sure that whatever existing infrastructure that you already invested is factored into the solution, helping customers save money.
Patching Limitations
It’s no secret that when it comes to patching applications for vulnerabilities such as SCCM or any other types of application deployment applications, in which case Zero Trust Connectivity proxy solution maybe questionable. After all with Zero Trust Concept some of our FusionTrust connectivity partners do not connect to the machines, but rather machines connect to connectivity partner. The way underlining patching applications behave is that they connect directly to devices on the network. Yet, the reality of it all with some of the FusionTrust connectivity partners, patching behavior must be in reverse. Meaning machines must connect to FusionTrust connectivity partner vs the other way around.
So what to do in this case? Does it mean companies should not migrate to Zero Trust Connectivity? Luckily not all hope is lost and there is a solution.
Solution to Patching Limitation with Zero Trust IoT Mobile Connectivity
Our company has created specialized solution just for the purpose of patching, where we can help companies with their patching needs, and not only help with their patching needs and make it compatible with one of our FusionTrust connectivity partners, but also simplify the entire process of patching and it’s complexity.
To learn more about our patching for vulnerabilities solution visit our FusionPatch solution offering.
FusionPatch is a separate service that our company offers for customers seeking to take control of their patching needs.
In combination with our FusionTrust Zero Trust Connectivity services and FusionPatch vulnerability patching services, customers can maximize their Enterprise security needs to the next level.
Other Zscaler Proxy Limitations
Not every application behave well with proxy type of zero trust architecture. For example when it comes to scanning for vulnerabilities using tools like Nessus, certain steps are needed to be done in order to make scanning for vulnerabilities work.
Luckily not all hope is lost. Our company also specializes in Vulnerability Scanning solutions, helping companies with scanning their external and internal network for vulnerabilities, conveniently delivered to you as part of our FusionScan service offering.
FusionTrust combined together with FusionScan and FusionPatch, can help companies not only get transitioned into Zero Trust Connectivity type of architecture helping companies stay secure, but can also help companies stay compatible with scanning & patching vulnerability tools as well as maximizing their enterprise security to the next level.
To learn more about our FusionPatch and FusionScan security offerings visit this link.
Licensing cost Analysis
When purchasing any type of equipment or software solutions relevant to firewalls, or VPN termination devices there are always licensing fees.
We can help you analyze these licensing fees and pick the right partner for your connectivity needs.
We are vendor agnostic
It doesn’t matter with which vendor you are dealing with of your IoT mobile connectivity need, we are vendor agnostic.
- Some vendors may be better than others when it comes to IoT mobile connectivity solution needs.
- Our role is to recommend the best vendor to help you save money while improving security.
- Regardless if you are looking for firewall in the cloud solution or Zero Trust type of solution, we can help you integrate it.
Our professional IT Consultants don’t just speak the vendor language, but rather speak the protocol language.
Think of it this way every vendor who builds some type of solution is relying on some type of protocol to make the solution work.
Our company has specialized IT Network Consultants who are well versed with both on-premise and cloud types of architecture, regardless if it’s AWS, Azure, Google.
Why connect IoT to the cloud?

Problem
Connecting IoT devices using legacy VPN solution providers network by network is complex.
Traditional VPN firewall vendors is difficult to manage, rules need to be created based on network, thereby allowing unnecessary access to other neighboring devices on the same network.
Managing these networks over time can be a lot more complex than managing SaaS based Zero Trust Connectivity type of style of network, simply because you do not have to worry much about underlining infrastructure.
With SaaS based IoT connectivity offering.
No need to worry about infrastructure complexity. All of the infrastructure that is being used gets managed through the cloud using SDN (software defined networking).
Process of allowing access to applications is simplified.
Problem: Connecting IoT devices to the cloud is not so easy
Depending on which type of IoT device your company has it may or may not have capability to have fully blown VPN agents installed directly on it, due to not enough memory or hardware capacity.
Installing traditional based agents may not be possible.
In such cases separate Mobile routers are being used with specialized modems to allow access across multi cellular ISPs, yet managing these routers and interconnectivity from your IoT device to these router all the way to the cloud is not exactly easy.
Solution
With our FusionTrust IoT Mobile connectivity service we can help companies design their mobile wireless network based on your IoT use case.
Some companies don’t require heavy type of architecture that other companies do.
Some companies perhaps have a tracking device that they want to monitor and connect to cloud to get minimum amount of data once every hour for example and don’t need anything else, while others may have more complex connectivity needs.
Regardless what your connectivity need is… we can help you make that need reality, with our customized FusionTrust IoT mobile connectivity service.
Many applications are not proxy friendly making it uncomfortable for companies to migrate.
Often many applications that require an advanced level of connectivity are difficult to connect over proxy.
That is because some of them are simply not compatible with proxy-based redirection. Trying to figure out what is compatible and what is not… can be challenging, requiring an advanced level of networking and security and application debugging expertise all in one type of problem.
Something that not exactly every company has time or employees to debug. In Zscaler there are multiple methods to bypass specific URL or applications, but not every application has the same fix.
Some apps no matter how much you try to make them work simply won’t work over Zscaler.
Some applications are home-brewed and using library dependencies that may not exactly be user-friendly with proxy types of connectivity.
The last thing you want to do is open up access to the entire GitHub when dealing with issues like this.
That is not to say that all hope is lost. The Zero Trust connectivity model simply needs to be adjusted for your existing enterprise.

Solution
Use FusionTrust IoT Mobile Connectivity Services
Zero Trust Connectivity for Remote Users and Machines
With FusionTrust IoT Mobile connectivity services, your company can get easily interconnected. Making it possible for IoT devices or remote access users regardless if they are located in a remote office or at home be able to easily connect to your office infrastructure onsite or on-premise.
Plus with FusionTrust connectivity partner monitoring solutions we can help customers monitor their IoT devices health connectivity.
Our company DBA Binary Fusion can help your company get integrated with FusionTrust connectivity partners helping your network get interconnected, regardless if you have 10 or 20 offices or 100 and regardless if you have 10 users or 1000 users.
Connecting Proxy based apps does not have to be difficult
DBA Binary Fusion can help you reverse engineer applications that require an advanced level of proxy-based connectivity and create permanent solutions as well as workarounds keeping your networks secure.
To Learn more continue reading this page.
Typical Example of what our customers ask us to do
Remote Access Connectivity Use Case
We get some customers who reach out to us and literally ask to see if we can help their IoT devices in the field get connected, while in motion.
- Problems that we instantly see is that customers have different types of enterprise architecture, with scattered AWS accounts, and VPCs not being connected at all between one another, relying on archaic policies that are very difficult to maintain.
- To solve this problem, we analyze each of the existing AWS accounts, to see what type of security policies are being allowed, what existing VPN solutions are being used to interconnect these VPCs and simply add a connector in each of the VPCs where applicable.
- In some cases customers have already existing Virtual Private Gateways interconnecting multiple sites together, other customers may have transit gateways with CSR peering through DMVPN network to on premise locations, and some don’t have anything at all.
- Whatever the case maybe, as part of our FusionTrust connectivity service offering we evaluate each of the applications, and create granular policies allowing connectivity access for each of the applications on granular basis, utilizing FQDN only as part of the best practices (no IP Addresses, unless absolutely necessary in occasional here and there types of exceptions).
- Some customers have tons of IoT devices that they want to connect and don’t know how, while others simply want to have secure communication to their AWS cloud over FusionTrust connectivity service .
Whatever the case is for every problem there is a unique solution.
- In the case of customers with AWS cloud architecture, we simply add connectors into AWS cloud, and get them to talk to FusionTrust connectivity partner cloud.
- Then after doing so, create necessary routing/filtering/translation rules and using source anchor forwarding or any other methods to connect customers to their internal and externally facing websites from IoT devices that happen to be in motion or in place.
- At the end of implementation customer’s employees has remote access connectivity to AWS resources and easy way of connecting from home while staying secure while browsing sites.
Additional Services for Identity Validation and Network Monitoring
In addition to our FusionTrust connectivity servicing offering, our company also offers multi factor level of validation across either certificates or other validation characteristics helping your IoT devices stay secure. After all, FusionTrust service is all about making sure that the person/device/machine that gets onto your network can be trusted. Implementing SaaS based offering by leveraging Zero Trust Architecture is one thing, but maintaining it and ensuring that authentication is granted for only authorized employees is a totally different ball game.
- After all, when connecting IoT devices or remote employees or machines to your cloud or on premise network, and recognizing who the employees are requires relying on some sort of multi factor level of validation intermixed with all sorts of bells and whistles, making it very difficult for many customers to wrap their mind around for how to actually do such level of integration.
- Primary reason behind such complexity is the simple fact that there are way too many types of devices, and way too many types of operating systems to keep track of that requires validation prior to getting on customer’s network.
- Luckily our company has created specialized service offering specifically for customers who are looking to fortify their IoT Mobile FusionTrust connectivity with multi factor level of authentication for different types of devices.
After Implementing Zero Trust Connectivity, do you think you are done?
Not even close….
After integrating FusionTrust Connectivityby leveraging one of our connectivity partners.
You also need to monitor the entire architecture, absolutely every single factor associated with the deployment of FusionTrust connectivity including multi factor authentication process, connectors, and entire enterprise for health of application connectivity and your users, which to be honest is not exactly straight forward or no where trivial endeavor.
Luckily not all hopes is lost. Our company specializes in Enterprise Monitoring Solutions helping your critical infrastructure get monitored.
We also can help companies visualize their entire environment with one of our FusionSmart monitoring connectivity partners such as New Relic,DataDog, LogicMonitor, SumoLogic, AppDynamics, Zenoss or Splunk, Solar Winds or even in a unified portal our custom made solution called FusionView
With FusionView solution IoT devices running on micro-services invoked by serverless lambda functions or other means can be easily monitored.
With FusionView there is greater flexibility for companies seeking to monitor their IoT Mobile Connectivity, especially if other monitoring tools on the market are too expensive.
FusionView software is part of our FusionSmart service monitoring offerings, but happens to be an actual software that is built based on your existing IoT network.
Our FusionView software is a unified portal that is customized to your visualization needs, without costing you arm and a leg.
For more info visit our monitoring services.
With FusionTrust IoT Mobile Connectivity Imagine This.
- With the help of our multi factor validation service offering FusionAuth, our FusionTrust consultants can help you validate your existing IoT devices prior to devices getting connected to your network.
- Imagine being able to visualize your FusionTrust IoT mobile connectivity and it’s underlining dependencies. With the help of our FusionSmart service we can accomplish just that.
- Imagine being able to visualize business transactions associated with your FusionTrust connectivity as well as infrastructure components.
- Imagine being able to visualize distributed tracing patterns as users navigate through different types of business transactions and how overall health of your application depends on the infrastructure components, application components and other dependencies.
- Imagine being able to visualize even complex recurring events that need to be factored into alerting, but require intelligent logic adjustment.
- Imagine being able to suppress alerts and tackle seasonal type of data, in order to minimize risk of not being alerted when you needed vs when alert is not really needed.
- Imagine being able to have predictive and forecasting monitoring that can combine previous cyclical data in combination with other factors that are relevant for your environment and be able to get alerted on that.
- Imaging having different types of dashboards for compliance, operational level and many other levels, in combination with repots being sent to you or other team members helping your team minimize risk and look like a super hero.
Imagine being able to interconnect offices and remote work force or IoT devices across multiple clouds.
Imagine being able to see individual user’s intermediate hops between each hop and see the health state of the applications that they are using.
Well with so many imaginative points... described above, you do not have to imagine anymore.
Simply reach out to our DBA Binary Fusion company tell us your use case and we’ll hit the ground running supplementing your existing IT Staff with super charged monitoring and cyber security expertise, that can help your organization reduce risk and best of all tackle complicated tasks that otherwise would not be possible to tackle without a strong IT Security and Network/Application monitoring expertise.
When contacting us, simply let us know the use case you are working on, what you are trying to integrate, what you need monitored, how you are trying to integrate, what tools you already invested and need help with. Or simply describe the challenge you are facing. Our company is very agile and flexible in the way we conduct business. If interested in our services feel free to reach out to us, so we can share with you some of our service offering demonstrations and see if we can do POC or POV for you.
We work with financial organizations as our core expertise, but also service other types of industries ranging from real-estate, manufacturing, professional LLCs, accounting firms, health/medical dental, entertainment industries and other types of industries.
In Summary
- Implementing Zero Trust Connectivity can be very challenging and almost impossible to configure without advanced knowledge enterprise architecture.
- With our customized FusionTrust solution offering, our company makes the complexity fade away.
- Picking DBA Binary Fusion as your company’s IT resource for advanced type of Security and networking integration will help you save tons of time, doing it yourself.
- With so many moving pieces it’s easy to get started doing it yourself and end up being stuck couple of months later.
- Luckily with our customized FusionTrust connectivity service offering you do not have to tackle this on your own.
- Even if you do not need the full managed FusionTrust service offering and only need small part of the service or any of the brother and sister services, such as FusionView, FusionAuto,FusionPatch, FusionScan,FusionML, don’t hesitate to reach out.
- Our company can create customized solution offering just for your specific enterprise need.
- Reach out to us, let us know your use case, we can get together analyze what you have, and provide your recommendation on how to move forward with what tool, what to monitor, how to monitor it and can also provide you presentation for some of the services that we did for our other customers in the field of Machine Learning, Certificate LifeCycle Management, Network Monitoring and beyond.
- If interested send an email to [email protected] or send us a message from the chat icon or fill out the form or call us, and simply let us know your use case.
- Thank You for taking your time to read about our FusionTrust Services.
Industries We Service and help customers integrate Multi Factor Solutions
Travel and Aviation
Consulting
We help companies monitor Airport Networks and ATM devices, as well as wireless access points.
Financial Services
Consulting
Our company helps Loan Processing firms, Banks, and other financial institutions monitor combination of both on premise and in cloud resources.
Education
With Entuity we can monitor Campus networks for real time changes on infrastructure such as firewalls, routers, switches, SDN controllers.
Law Firms
We also work close with Law Firms and other types of legal organizations seeking to monitor their cloud and on premise resources.
Manufacturing
Our company can help customers add foam spray pumps, or any other types of manufacturing devices, or IoT devices into Entuity monitoring software.
Accounting and CPA firms
Our company helps CPA accounting firms monitor their network for newly discovered devices, and changes in data.
Alternative Connectivity Solutions that we can work with
We can help customers with their UTM and Sophos XG or other firewall models get connected to AWS cloud.
We can work with Cradlepoint IBR routers and other types of cellular routers to help you create SDN solution with direct access to the cloud over OpenTLS.
We can help your company have secondary level of remote IPSEC access directly to Pulse Secure Appliances installed in the form of AMI in AWS cloud.
We can help customers get integrated with Zscaler as primary method of communication for remote access VPN, with combination of some other vendor like Pulse Secure in AWS as secondary vendor.
We can help customers create VPN tunnels through transit gateways to CSRs hosted in AWS cloud from the remote branches and we can help run EIGRP over DMVPN tunnels or even OSPF.
We can work with GAIA R77 and up version appliances helping customers get connected to the cloud in either routed or policy based routing way.
We can help customers with Cisco ASA connectivity to AWS cloud, using active and standby type of fail over methods.
We can help with Edgerouter connectivity from behind the NAT devices.
We also work with customers who have FortiNET environment and seeking help to interconnect their on premise networks to AWS cloud either through built in native features of AWS using virtual private gateways or to Fortigate Appliances in AWS cloud.
Problems and FusionTrust Solutions
Maintaining VPN tunnels is complex, although understandable in a complex multi cloud environment. Instead FusionTrust connectivity can be used, where your company would rely up on Zero Trust Architecture for inter-connecting your networks, and our company can help you integrate such architecture, either with Zscaler or another type of vendor, whomever is most affordable for your organization’s budget.
Our company can help you dissect cost factors and evaluate multiple vendors for your connectivity needs, including the vendors that you may already be engaged with, providing that they are based on Zero Trust Architecture. (if not than we offer separate consulting connectivity service offering for such cases)
Indeed, not every application is compatible with proxy. However our consultants can assist with deciphering your existing applications, to see if they could be made compatible with Zscaler Proxy. Either through the process of bypassing it, or application re-architecture, or modification of connectivity architecture through alternative means of connectivity beyond Zscaler such as your secondary VPN solution provider working in parallel with primary FusionTrust connectivity solution.
- Luckily there is no CA associated with Zscaler, Zscaler acts like a CA, when it comes to generating keys and associating them with Zscaler connectors.
- However, that doesn’t mean that you should just forget about certificate management.
- There is still certificate lifecycle management concept being involved just like with every thing else.
- Last thing you want to do is forget about renewing your cert.
- Our CLM and PKI solutions can help your company fortify your FusionTrust connectivity by ensuring that the certificate lifecycle is being managed and not forgotten. and certs are renewed regardless if it’s for individual connectors or for SAML based authentication or any other types of infrastructure that may exist in your enterprise beyond Zscaler. To learn more about our CLM and PKI solution offering visit this link.
- Indeed when it comes to FusionTrust connectivity there are other factors that can exist in your environment that may bock such connectivity such as NACLs or inbound or outbound security groups.
- Not to mention other factors that may exist in your environment, ranging from CrowdStrike agents on laptops, to Zone Based Firewalls on the routers, and Intrusion Detection or IPS types of connectivity restrictions configured on customer’s firewalls.
- Managing and seeing all of these connectivity restrictions is the key, after all FusionTrust connectivity relies on the underlining connectivity sort of like BGP relies on already pre-established connectivity prior to being connected on port 179 over TCP.
- Luckily our company can help companies visualize connections that are getting blocked across entire layer 1 through 7 stack through what so called FusionView unified portal, visualizing multiple types connectivity restrictions across your entire enterprise.
- Together with FusionTrust and FusionView the process of identifying what is being blocked where, becomes extremely simplified.
- Alternatively our company can help customers integrate many of the security systems that are responsible for blocking access with customer’s existing SIEM regardless if it’s Sumo Logic, Splunk, ELK stack or other.
Indeed any time application gets patched, it’s possible that after patching some new FQDN names get introduced or original URL where the application was hosted out of a sudden stops working, causing users not being able to connect to application.
- Luckily as part of our FusionPatch solution offering, our company verifies application health state after the patch is complete. Hence not only do we deploy patching solution architecture, we help you maintain it it’s health state.
- Our FusionView unified portal can help customers visualize application health state, before and after patch deployment.
- Our FusionTrust consultants can help your company reverse engineer application connectivity needs to see if it can be proxy compatible.
- In cases if the application is not proxy compatible, it can either be bypasssed or escalated to our App development team to help you customize architecture of the application that you are using in order to make it compatible.
Other Integration and IT Services Similar to FusionTrust service
-
AlphaCICE & Alpha FusionView Service Details
Read moreMinimize false positive, duplicate alerts with AlphaCICE central intelligence correlation engine. AlphaCICE and unify all of your tools AIOPS events in a single pane of glass with Alpha FusionView. See how Alpha FusionSmart Enterprise Monitoring service that Alpha Technologies offer ties it all up together in context of multiple ITIL best practices phases.
-
AlphaCICE – Central Intelligence Correlation Engine
Read moreMinimize false positive, duplicate alerts with AlphaCICE central intelligence correlation engine. AlphaCICE is a custom solution and service offered by Alpha Technologies that is specifically designed for financial industries seeking to take control of their incident management process. Incident Managers can maximize their operational effectiveness through streamlined operationalized workflows, by relying on correlated supervised and unsupervised AIOPS classified intelligence fetched from your already existing monitoring tools. AlphaCICE is explicitly designed to reduce multiple events into a single actionable event that matters most, by empowering data owner operators with prescriptive & AI & ML driven recommendations
-

Alpha Digital Transformation of Applications & Tech Stack
Read moreAlpha Digital Transformation solutions for all size businesses seeking to secure their legacy application in order to minimize risk, while in parallel migrate the application and tech stack into modern API invokable and event driven ecosystem helping data owners get closer to their data.
-

Alpha AWS | AVD | Office 365 Virtualization Solutions
Read moreAWS Desktop and Network Virtualization solutions and services for small, medium & large size companies seeking to solve high latency connectivity related problems, while maximizing security.
-

Alpha FusionChain Innovative Solution for BlockChain Database and Monitoring
Read moreMigrate Your Legacy applications to Blockchain faster and safer without disruption of the existing workflow. With our tool kit we can help companies build, deploy maintain and manage Blockchain architecture helping you revolutionize your microservices and decentralized architecture. We can build Blockchain networks for multiple use cases ranging from NFTs, Crypto, MetaVerse and beyond.
Other Solutions & Services that we offer
Why Customers Pick Us

Automation of Applications
Automation of monolithic and microservice types of applications, software testing and quality assurance. Helping companies minimize manual tasks in every day operations and reduce costs by leveraging custom built automation scripts for your enterprise infrastructure, ranging from automation of APIs to orchestration of complex resources.
Read More
Expertise in Cloud and On Premise Environments
Expertise in AI and ML with multiple clouds AWS, Azure, GCP, Kubernetes, Serverless Lambda Functions, Docker containers, and beyond as well as on-premise network & app infrastructure environments.
Read More
Unified View
Custom-built view bridging your micro-services and monolithic application, infrastructure, and monitoring need all in one portal. For example, ServiceNow, Jira, CMDB, BMC Control M and Microservices all in 1 portal, helping customers visualize, slice, and dissect data as well as create reports, trends, and forecasts, based on results of any data, either coming from your on-premise or in cloud environment
Read More
Based on Zero Trust Connectivity Architecture
Get your on site locations and remote office work force or IoT devices connected with the help of custom solutions designed to keep companies secure, while protecting employees form malicious threats.
Read More
FusionCLM PKI Solutions
Certificate Lifecycle Management (CLM) and PKI services and solutions for companies seeking to take control of their certificate validation and enrollment needs, helping companies reduce risk
Read More