
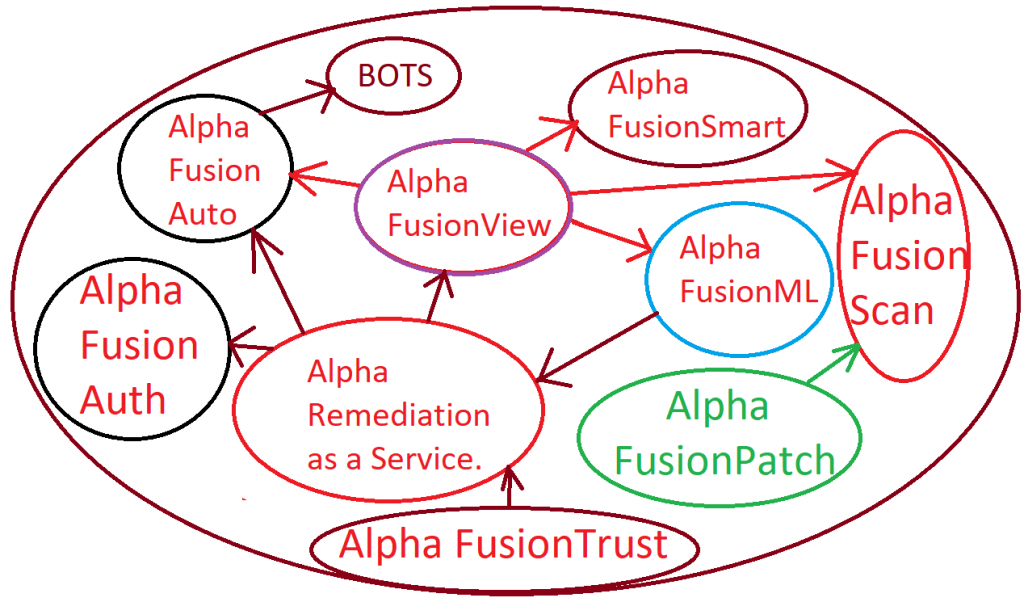
Our company offers, customized IT solutions for different types of organizations seeking to reduce risk, secure their enterprise, maximize return on investment and best of all save money.
- With Alpha FusionAuto we can help companies create customized automation workflows for in house applications, networks, machines and devices across cloud, on premise or hybrid environments.
- Our Alpha team specialize in creating automation Bots that can run and do manual tasks that would take a long time otherwise.
- One way we do this is either with your very own automation tools that your company may have already heavily invested in such as UI/Path, Control M, Mulesoft, Ranorex or any other tool.
- Or with our very own Alpha FusionAuto Tool Kit consisting of multiple types of automation tools, helping your company automate your existing microservices architecture, network, infrastructure and business processes, therefore helping you save even more money on any of the existing vendors.
- Or alternatively combination of both Alpha FusionAuto tool kit and management of your existing automation vendor solutions.
With Alpha FusionAuto
- We can analyze your existing costs being spent on your automation vendors, and provide the proposal for how to reduce these costs, either by optimizing your existing automation tools usage, or by supplementing your automation tools with our very own Alpha FusionAuto tool kit
- We can analyze your existing workflow activities, and convert them into technical BOTS, then implement scheduled execution these BOTS, that will run the jobs and provide automatic reports.
- We can create automation jobs and self healing remediation jobs, that can be executed based on the dynamic nature of the environment.
- As part of our Alpha remediation as a Service solution, we can feed BOTS with insights gathered from, AI, NLP or machine learning data helping your BOTS continuously adapt to the dynamic data behavior changes.
- As part of our Alpha FusionView software we can visualize your automation results including all the relevant KPIs all in a single pane of glass.
- As part of our Alpha FusionML we can build custom machine learning models to detect anomalies, forecast on data and view entire transaction data chain associated with your automation jobs.
- As part of our Alpha FusionScan solution we can create customized jobs to conduct automated scan jobs to detect vulnerabilities.
- As part of our Alpha FusionPatch solution we can create automation jobs to conduct automatic patches of your systems and applications and feed the results into any other automated jobs.
- As part of our Alpha FusionTrust solution we can help your automated data transactions traverse your network securely, while helping your employees and contractors get connected to cloud or on premise resources from their home or office.
- Additionally we can create custom automation jobs for your Zero Trust Access environment, making it easier for your organization to keep track of employee’s connectivity health status throughout the entire transaction chain.
- Plus with our custom automation jobs we can help your SDN networks self heal.
- As part of our Alpha FusionAuth solution we can help your in office or remote employees and contractors get authenticated with certificates, while maintaining certificate lifecycle management by automating your certificates renewal process using our Alpha FusionCLM tool.
Our Alpha Fusion Flagship Solutions
Automation Software

Here is what Alpha FusionAuto can automate




In addition to automating workflows with Alpha FusionAuto Tool Kit we can also create custom automation scripts for integration with any of your network infrastructure, that includes cloud and on premise infrastructure.
We can automate and visualize in a unified view your critical connectivity infrastructure.
Our company works with different types of vendors, ranging from Sophos, Fortigate, Checkpoint, Cisco, Ubiquiti, Splunk including Zscaler and many other vendors helping customers automate and interconnect their branch offices to AWS or Azure, GCP clouds as well as visualize critical KPIs in Alpha FusionView.
With the help of Alpha FusionView software we can help companies visualize wired and wireless connectivity of remote and in office users. Additionally we can visualize workflows and critical KPIs that attributed to employee’s performance and application health status.
We Automate Visualize & Help You Manage your data
In addition to automating and visualizing infrastructure related data with Alpha FusionView we can visualize containerized micro-services and monolithic types applications, in combination of different types of business KPIs fetched from customer’s CMDB like Device 42, ServiceNow or others.
To learn more about our other sister services related to Alpha FusionAuto please see the slider below.
With Alpha FusionView software we ingest data, then slice it and dice it, pre-process it and ensure that the critical data is hashed or masked, helping companies standardize their data set in the form of unified dashboards split by department, impact, productivity, and other types of characteristics.
Our software can be adjusted per customer requirement, per specific workflow or set of workflows and can accept data from different types of data sources .
Alpha FusionML tool is an extenuation of Alpha FusionView tool except what it offers additionally is visualization of KPIs based on advanced AI, machine learning, natural language processing, forecasting and anomaly detection.
With Alpha FusionML we can help companies not only detect anomalous activities based on customized supervised or non-supervised machine learning models, but can also help companies inter-linking these anomalies through the chain of events based on geographical factors or any other type of data chaining functionality explicitly designed to help companies trace the original request or transaction, helping customers identify problems quicker.
Our team of data scientists and data analysts as well as network consultants and data integration experts work together side by side with your company’s data subject business experts to identify critical KPIs, pre-process data, build machine learning models, train and automatically retrain them helping companies identify trends and reduce risk.
Alpha FusionML is a separate module that gets deployed side by side with Alpha FusionView. This module allows us to train models based on different types of algorithms and run these models, and integrate results form these models directly in Alpha FusionView unified portal.
The best part about Alpha FusionML is that we don’t just build random models within the tool, we build models based on customer’s use case.
If you would like to learn more about Alpha FusionML solution contact us to receive more info and a customized presentation.
With Alpha FusionSmart solution our company helps organizations visualize their enterprise using already pre-existing tools that the organization may already have.
For example tools like DataDog, Splunk, SumoLogic, AppDynamics, Zenoss, Splunk, DynoTrace, NewRelic, SolarWinds, MuleSoft, Control M, Tableu, Power-BI, Logic Monitor, Entuity, Zscaler, Fortinet, Jira, Confluence, ServiceNow or other types of CMDB tools or Cyber Security tools such as CrowdStrike, Okta or others.
While working with different tools, we can help companies optimize their tools, minimize data ingestion costs and unify it all in Alpha FusionView single pane of glass helping companies visualize their entire layer 1 through 7 connectivity.
To learn more about our Alpha FusionSmart Enterprise Monitoring Solutions contact us to received customized presentation to see how we can help you take control of your environment, save money on already invested tools, while at the same time help you unify your KPIs in Alpha FusionView.
Monitoring web transaction logs and who visits what site, how long the person stays logs in, when they logged in and what applications they visit, is solely dependent on customer’s network architecture.
With Alpha FusionTrust Connectivity Solutions we can help companies transition to ZeroTrust Architecture, secure & simplify their remote and in office connectivity or alternatively help companies manage their existing Zero Trust Architecture and multi cloud environment.
Secure connectivity means greater control and application level visibility.
By enrolling into our customized Alpha FusionTrust solution customers get the benefit of both, ability to further increase security, simplify their traditional VPN connectivity and gain unified visibility of their in office or home employees directly in Alpha FusionView single pane of glass portal.
To learn more about our Alpha FusionTrust solution and request customized presentation to see how we can help you transition to Zero Trust Architecture maximize visibility and reduce risk contact us for details.
Additionally for customers seeking to connect their enterprise together with IoT or any remote employees we can also show you how to do that without spending a lot of money on full scaled solutions. With our Alpha FusionLink client we can help companies stay connected to their cloud and on premise environment using Zero Trust Architecture.
Alpha FusionLink client is part of our Alpha FusionTrust solution.
With Alpha FusionAuto solution our company can help organizations created customized BOTs and automated scripts that would reduce manual overhead. Plus if your company already has any existing automation tools we can help you manage them, and save costs.
Automating is done based on
Best Practices Frameworks
We have created our own automation frameworks that makes it easier for us to create customized automation jobs while minimizing costs. Additionally we follow best framework practices that many automation tools already utilize.
Automation Tools we use part of our tool kit
- Depending on the environment that we are working with and the use case tools may vary.
- For example tools we use are Ansible, Chef, Puppet, Terraform or Nornir
- Depending on the customer’s environment our tool kit is adjusted to match and enhance customer’s environment.
- Some of the tools we use directly integrated in User Interface of Alpha FusionAuto tool kit.
- The languages we use also depends on the use case, but we have in house expertise for different type of languages, such as Java, Ruby, Python, C++, etc.
Translating Business Requirements Requirements for Automation
- Part of our Alpha FusionAuto solution is to gather data, but even before gathering that data what we do is assign business analyst who works with customer’s existing team.
- Our automation business analysts are well versed in understanding automation processes and how to translate manual workflows into automated BOTS.
- Additionally we have actual experts who create the scripts and automated bots, across both Alpha FusionAuto tool kit and across customer’s existing tools.
Microservices Automation
- With microservices automation, our Alpha team can help companies automate their microservices transactions across different clouds.
- Now days many applications are migrating to microservices, yet organizations are still lacking adequate automation practices.
- Regulating microservices workflows and workloads is part of our Alpha FusionAuto solution.
- Regardless if you are running microservices environment, in cloud or on premise, our Alpha FusionTool Kit can morph to your environmental needs.
- In addition to automating customer’s microservices architecture, we can even monitor it all using customer’s existing tools that company’s may have already invested. To learn more about this service check our Alpha FusionSmart solution to see how we can help you reduce risk and save money.
Alpha FusionAuto Use Cases
Imagine needing to automate and visualize your entire infrastructure landscape side by side with application performance and business transactions in order to identify which employees logging into company’s network, when how and for how long.
With Alpha FusionAuto we can help automate your Zero Trust Architecture
Imagine automating Kafka nodes with your existing Zero Trust Architecture
- For example we can create automated scripts that automatically populate application access policies from Kafka brokers.
- When user request goes to Kafka, Kafka brokers relay the request to another name, yet it’s not always possible to know what the name is.
- With Alpha FusionAuto we can create custom automation scripts that makes it possible to unify process of creating Kafka nodes while simultaneously updating Zero Trust Architecture policies in your existing vendor or directly in our very own Alpha FusionTrust solution and therefore allowing automatically access for your Kafka hosts…
- Additionally we can create different types of automated API calls that directly interact with our Alpha FusionTrust solution for your company’s connectivity needs.
Automate User Interactivity and how busy the employee is
Imagine automating your user interactivity and interconnectivity. Each workflow is different, and sometimes is executed by the user or sometimes by the system process on behalf of the user. With Alpha FusionAuto we can automate these processes and then visualize them in Alpha FusionView.
- Interconnectivity between in office employees and your identity systems such as Cisco ISE, OKTA, environments.
- Interconnectivity between remote employees and your already existing Zero Trust Connectivity vendors.
- How long it takes for user to stay logged into your Zero Trust Architecture.
- What applications and websites users browse.
- How many times screen went into sleep mode.
- What tickets users created.
- What internal pages they accessed.
- How many collaboration tools they logged into.
- How many total key strokes and mouse clicks user executed by date.
- What switches/routers/devices user logged in and what changes were done.
- How many emails sent, and change controls executed.
- How idle the user is on Teams or Zoom or other types of collaboration software.
- Location of the user and trend of activities over time.
Helping companies automate critical functions responsible for different types of workflows and visualize employee productivity based on department, work from home or in office type or other criteria.
Automate Results of Desktop Tools accessed by employee
With Alpha FusionAuto we can help automate Desktop/Laptop tools accessed by employee as well as commands that were executed by employee, and with Alpha FusionView we can visualize all of these automated results in a unified view.
- What commands user typed in command prompt.
- What processes utilized the most.
- What types of connections initiated.
- What type of installations attempted.
- User Login Failures
- Applications accessed.
Automation of Enterprise Functions
Full infrastructure automation and visualization of your enterprise architecture. Here are some of the functions we can help automate with Alpha FusionAuto.
- Automation of Enterprise Applications APIs using tool like Mulesoft.
- Automation of enterprise business functions using Control M.
- Creation and automation of RPA BOTs.
- Zero Trust Connector Health Monitoring for CPU, Memory, connector health status, and beyond.
- Application Health Functions.
- Health Monitoring of User connections.
- Web & Advanced Firewall connectivity.
- Switch/Router/Firewall Load balancers commands.
- Automation scripts for ServiceNow in prep for integration with SumoLogic or Alpha FusionView.
- Custom automatic processes that produce log data so this way results from the BOT logs can be used in Dashboard Creation for AWS Workspace, Azure, AVD, Zscaler ZIA, ZPA, Authentication or any other type of KPIs, side by side with business transaction monitoring.
- Automation of agent instrumentation for servers, and other types of devices.
Cloud Infrastructure Automation
First-time setup and continuous support.
- Creation of advanced types of automation application integrations and creating automation workarounds and permanent solutions while unifying automation results in Alpha FusionView
- Automation of AWS, Azure, and Google Clouds resources, ranging from Ec2 instances, nodes, clusters, application load balancers, gateways, proxies.
- Automation of Serverless functions.
- Automation of Single Sign-On, IAM systems and visualization of SCIM, SAML authentication attempts.
- Automation of collaboration applications such as Teams, Zoom, AWS Workspaces, Azure AVD, etc, and others.
Cyber Security Automation
- MITRE & ATT&CK automation for identification of threats and elevated risks.
- Automation of continuous scans and patching solutions.
- Automation of threat detection activities.
- Automation of cyber security playbooks.
- Automation for identification of exploits.
- GDRP,NIST, ISO 27001 Standards automation in relationship to vulnerabilities in Alpha FusionView
- Vulnerabilities visualizations in Alpha FusionView fetched from our customized Alpha FusionScan solution.
- Patches visualizations in Alpha FusionView fetched from our Alpha FusionPatch solution
Educational & Knowledge Transfer
First time and continuous driven effort.
- Educational Playbook Generation for company employees ranging from regular users, IT staff, and beyond.
- Creation play books, and escalation procedures in confluence/SharePoint for business and infrastructure types of applications.
Professional IT Consulting
For Small Large & Medium Size Businesses
Alpha FusionAuto Consulting services for any automation use case
How we can help
Alpha FusionAuto
Packaged automation solution for companies seeking to automate their data set using either already existing tools or with the help of our Alpha FusionAuto Toolkit.
Read MoreTop 3 reasons why not to skip on Automation
Reason 1: Saving Money
One way of saving money is by automating repetitive activities.
- Did you know that certain activities such as for example user constantly being locked out can be automated without necessity for service desk to spend time on additional manual task.
- We can help companies identify these repetitive manual activities and convert them to automation jobs.
Alpha FusionAuto can help companies save money by automating manual workflows.
Reason 2: Minimize Risk
One way of minimizing risk is by conducting certain automated activities on regular continuous basis.
- For example vulnerabilities often found on multiple devices, automating scans that discover these vulnerabilities on regular basis is the key. Running one time scan per year is no longer adequate any more.
- Another example is for machine learning models, data constantly change, and when it changes machine learning models must adopt to continuous changes.
- With Alpha FusionML our company helps create custom anomaly detection algorithms, data forecasting, natural language processing and machine learning.
- However after such algorithms are created they need to be automated so machine learning models constantly learn and re-learn the environment in order to produce more accurate results.
- This requires automation of such models. Without retraining the models on automatic basis, there is a risk factor for missing anomalies.
- Other example of reducing risk include updating certificates on devices, where the process of remembering for how to do so after many years passed by can be complicated.
- Not renewing certificates on critical systems can result in downtimes and major outages.
- Relying on manual processes to renew certificates places additional stress on employees, considering the fact that there are many applications for which certificates are needed, and processes for importing these certificates always different.
- With Alpha FusionCLM certificate lifecycle management solution we can help companies automate their certificate enrollment with the customer’s PKI.
Reason 3 Improve Productivity
One way of improving productivity is by offloading low hanging fruit items into automation life cycle vs doing time intensive functions manually.
- For example, let’s say your employees are constantly reconciling data between website and let’s say some spreadsheet. and that happens regularly.
- With Alpha FusionAuto we can create custom BOTs that scrape content from the internet, feed it into a file and perform comparison between spreadsheet and the downloaded content from the internet.
- Doing so saves times simply because now employee can be productive doing something else, other than doing the same thing manually.
- Additionally as part of our Alpha FusionAuto solution we can work with customer existing tools like Uipath or Control M to create automation workflows to further automate workflows and can help you manage these tools.
Cost Analysis & Savings on Existing Automation Tools
- When many of our customers reach out to us, rarely does every customer know all the associated costs with the solution, simply because there are many factors associated with automating critical processes.
- As part of our Alpha FusionAuto solution offering, we help customers pick the most optimal cost-effective options for their data automation needs.
- For example if customer has UIPath and paying too much for this vendor, we can evaluate what functions are being automated and customize our Alpha FusionAuto tool kit to meet the need for only for these specific functions.
- After all why try to kill a fly with a gun, when there maybe more cost effective way of achieving the same results.
- Many automation companies out there try to sell solution that have absolutely everything, yet the reality of it all, only small sliver of the solution is actually needed.
- With Alpha FusionAuto ToolKit we hand pick the features that are truly needed for your use case to make your solution tailored towards your business need, and utilize these features from our already developed frameworks.
Licensing cost Analysis
When purchasing any type of data automation software there are always all sorts of licensing fees, we help you dissect these license fees to make the most optimal decision making. While substituting some of the functions with our very own features within Alpha FusionAuto ToolKit.
Imagine using your money for other needs instead of spending it on expensive licenses.
We are vendor agnostic
It doesn’t matter with which vendor you are dealing with, we are vendor agnostic.
- Some vendors may be better than others when it comes to individual solution needs.
- Our role is to recommend the best vendor to help you save money
- Regardless if you are looking for full automation solution or open source solution, we can help you craft one up, and also can work with your existing vendor to automate workflows and BOTS that your staff already started automating.
Our Alpha Team don’t just speak the vendor language, but rather speak the protocol language.
Think of it this way every vendor who builds some type of solution is relying on some type of protocol to make the solution work.
Automating manual tasks can be real hassle.
Problem
Automation is rarely static
Automating even simple activities within ordinary workflow requires building the logic, and maintaining the automation process, yet the workflows often change without automation processes being updated.
Every workflow is different, hence the complexity behind automating such workflows.
For example some company’s have employees working in hybrid settings from home and in office.
Each employee have their own workflow and their own process for getting job done.
Some of these processes can be automated, yet if the workflow changes, and automated process not updated, then the automated job execution will fail.
It can be very tricky maintaining workflows, and updating BOT processes. besides some of the processes are dynamic in nature, meaning the workflow of the automation job may actually change depending on the nature of the workflow.
Tracking dynamic nature of the workflow and reflecting the results in automation bot… is not exactly walk in the park either….
Automating Jobs Requires Maintenance
Not every workflow can be automated, but the low hanging fruits tasks that can be automated often requires constant oversight and upkeep. This requires keeping track of what automation jobs are running up to satisfactory levels and what automation jobs are out of sync.
Creating Logic for automation jobs takes specialized skill
In many cases some workflows require complex data slicing and dicing as well as data analytics expertise and data extrapolation prior to being able to automate it. Depending on how the workflow interfaces with the applications, different languages may need to be used. Often many companies don’t have such vast level of multi lingual expertise in house.
Discovering Anomalies in Bots behavior can be very difficult.
Even when automation jobs are created, and maintained, extrapolating data out of the jobs, and making sense out of it in a visually appealing manner requires specialized data visualization platforms that can help companies not only visualize BOT activities, but can also help detect anomalous activities in the automation behavior. That requires building customized machine learning models which many companies simply don’t know how to do.
Discovering Anomaly is one Thing, but discovering what will happen next is another
Many companies who do end up being successful in creating automation tasks, and building anomaly detection around the KPIs associated with these automation jobs… often discover that not only do they want to discover anomalies in their data, but they also would like to forecast the behavior of such anomalies, by modifying KPIs and simulating what the behavior would look like or simply forecasting the data.
Forecasting and Anomaly Detection for automated workflows is one thing, but seeing an entire transaction data chain is another.
Even if specific workflows or behaviors were automated, and properly maintained, and even if machine learning models and anomaly detection mechanism were built, often many of the times companies want to know…. where the transaction originated from and what was it’s destination, and not only that, but what were the intermediate hops associated with the transaction.
Visualizing intermediate data chain requires end to end visibility
Even if automation job was successfully implemented and managed, gaining access to entire automated data chain path require specialized agent instrumentation. Unfortunately many agents out there are not exactly built based on Zero Trust Architecture, and often rely on traditional methods of VPN connectivity making data exposed and prone to man in the middle attacks.
Visualizing Vulnerabilities associated with automated jobs can be very difficult
We often find many companies automate their patches and security update, yet struggle to visualize trends for their vulnerabilities as well as cause and effect relationships after automation jobs were completed.
For example Every Vulnerability presents risk. If automated patch cycle ran, then vulnerabilities should be reduced. Yet visualizing such effect is not exactly trivial task.

Solution
Intelligent Job Automation Building
Alpha FusionAuto
With Alpha FusionAuto our company can help organizations take control of their workflow automation needs, by reducing complexity, minimizing expenses on manual tasks, and maximizing return on investment.
With Alpha FusionAuto solution our company can help with automation of home brewed applications, vendor solutions, network, infrastructure, microservices environments across multi lingual environments regardless where your app is running in cloud, hybrid, web, desktop, IoT, wireless, wired or anything in between.
Some of the vendors/products we work with include but not limited to Control-M, Ranorex, UI/Path and many others.
Single Pane of Glass Data Visualization all in one
Alpha FusionView
With Alpha FusionView our company can help organizations take control of their enterprise visibility, their network, infrastructure and critical business transaction data by visualizing results from workflow automation bots all in a single pane of glass, helping companies minimize risk and save money on other data ingestion tools.
Data Ingestion Cost Saving
Our company can help customers visualize their critical business data, including the results from the automation jobs, and have developed frameworks and processes for how to reduce data ingestion costs in comparison to other Data analytics tools. As part of our Alpha FusionSmart Enterprise Monitoring solution, our data analytic, and data science experts can help your IT staff aggregate data from multiple dates sources including the output data from your Automation Tools like Control M, UI Path, MuleSoft, Ranorex and others into our Alpha FusionView tool.
Machine Learning | Forecasting | Anomaly Detection & Data Chaining
Alpha FusionML
As part of our Alpha FusionML Solution offering we can help companies not only visualize their automated data output and show entire chain of events associated with that data, but can also help companies detect anomalies and conduct forecasting of important transactions, that can help companies spot abnormal behavior quicker, and get notified about it. Our Alpha FusionML Tool Kit integrates directly with our Alpha FusionView software.
With Alpha FusionML Solution our Alpha team can create customized machine learning models and create AI and NLP type of models that can help companies predict the automated job transactions behavior, or directly forecast the behavior of the automated transactions or directly influence the behavior for the automated transaction.
Customized Data Visualization Per each Automated workflow
Alpha FusionSmart
As part of our Alpha FusionSmart Enterprise Monitoring solution offering we can help companies slice and dice the data, and work with your existing business subject matter experts from each of the departments to create customized data visualization solutions per each department for each of your automation jobs, helping you utilize already existing tools that you may have in house to monitor the automation jobs.
By augmenting your existing IT staff with our very own Alpha team of experts, this way your internal IT/Business team can work with what they got, while getting additional help from our augmented Alpha FusionSmart Enterprise Monitoring solution helping you monitor your existing automation tools and any other monitoring in house tools.
Visualize Behavior of users and critical business transactions
As part of our Alpha FusionSmart offering we can help companies analyze many of the user’s behaviors and visualize the behavior in Alpha FusionView. For example some users constantly log into Jira to create tickets and some to ServiceNow, while others browse the web and do other tasks. We can visualize all this data and summarize it into intelligent views all within single UI>
Simplify Data Gathering & Reduce risk.
As part of our Alpha FusionTrust Solution offering we can help companies transition to Zero Trust Architecture maximize data visibility based on application connectivity rather than IP, and offload logs, Metrics & traces directly to our Alpha FusionView tool, helping companies visualize their data and employees a lot more effectively, while simultaneously offering a way for Zero Trust Security for your automated transactions.
Visualize Productivity of Hybrid Users
As part of our Alpha FusionAuth solution offering we can help companies implement identify, authenticate and authorize their employees and devices, in order to extract valuable insights for how user/machine is authenticated, where from, in office or out of office and visualize it all in Alpha FusionView helping you visualize employee productivity in office and out of office side by side.
Visualize Vulnerabilities and Their Resolution Trends
As part of our Alpha FusionScan solution offering we can help companies with scanning for vulnerabilities, and visualizing these vulnerabilities directly in Alpha FusionView helping IT Security professionals see results of the vulnerability scan, and with our Alpha FusionPatch solution we also help companies patch their devices and show results of the patched devices in context of Trends directly in Alpha FusionView helping companies reduce risk and preserve their employees productivity.
Typical Example of what our customers ask us to do
Remote Access Connectivity Use Case
Note in this use case you will see how multiple Alpha Binary Fusion solutions come together to help customer with specific issues, where Alpha FusionView happens to be small sliver of the solution offering.
We get some customers who reach out to us and ask to connect their work from home employees and 3rd party contractors to their on-premise and cloud networks.
- Problems that we instantly see is that customers have different types of enterprise architecture, with scattered AWS accounts, and VPCs not being connected at all between one another, relying on archaic policies that are very difficult to maintain.
- To solve this problem, we analyze each of the existing AWS accounts, to see what type of security policies are being allowed, what existing VPN solutions are being used to interconnect these VPCs and simply add a connector in each of the VPCs where applicable.
- In some cases customers have already existing Virtual Private Gateways interconnecting multiple sites together, other customers may have transit gateways with CSR peering through DMVPN network to on premise locations, and some don’t have anything at all.
- Whatever the case maybe, as part of our Alpha FusionTrust connectivity service offering we evaluate each of the applications, and create granular policies allowing connectivity access for each of the applications on granular basis, utilizing FQDN only as part of the best practices (no IP Addresses, unless absolutely necessary in occasional here and there types of exceptions).
- Some customers have tons of IoT devices that they want to connect and don’t know how, while others simply want to have secure communication to their AWS cloud over Zscaler or any other Zero Trust architecture type of vendor.
Whatever the case is for every problem there is a unique solution.
- In the case of customers with AWS cloud architecture, we simply add connectors into AWS cloud, and get them to talk to the Zscaler cloud or our very own custom built Alpha Fusion Trust cloud that we can build specifically for the customer to handle their Zero Trust Connectivity use case.
- Then after doing so, our Team creates necessary rules either over Zero Trust Architecture connectors using source anchor forwarding or any other methods to connect customers to their internal and externally facing websites using concepts of Software Defined Networking.
- At the end of implementation customer’s employees have remote access connectivity to AWS resources and easy way of connecting from home while staying secure while browsing sites.
- Additionally by leveraging Alpha FusionTrust Connectivity solution customers not only improved security of their enterprise, but also opened up pathway for getting additional help from our company with our Alpha FusionSmart solution offering that is explicitly designed to help customers continue utilizing their very own monitoring tools that they have already heavily invested in and unifying critical employee productivity data from multiple customer owned tools directly into Alpha FusionView software.
- By doing we help customer being able to visualize and monitor employee productivity fetched from multiple data sources including Zero Trust Connectivity resources containing data such as web connectivity logs, firewall logs, or any other critical application or infrastructure data.
- Across entire use case as part of Alpha FusionAuto solution we automate certain functions such as creation of VPCs, EC2 instance, invocation of server less functions, automation of APIs and a lot more.
Additional Services for Identity Validation and Network Monitoring
In addition to our Alpha FusionTrust connectivity servicing offering, our company also offers multi factor level of validation across either certificates or other validation characteristics helping your networks stay secure.
After all, Alpha FusionTrust service is all about making sure that the person that gets onto your network can be trusted. Implementing SaaS based offering Zero Trust Architecture is one thing, but maintaining it and ensuring that authentication is granted for only authorized employees is a totally different ball game.
- After all, when connecting remote employees or machines to your cloud or on premise network, and recognizing who the employees are requires relying on some sort of multi factor level of validation intermixed with all sorts of bells and whistles, making it very difficult for many customers to wrap their mind around for how to actually do such level of integration.
- Primary reason behind such complexity is the simple fact that there are way too many types of devices, and way too many types of operating systems to keep track of that requires validation prior to getting on customer’s network.
- Luckily our company has created specialized service offering specifically for customers who are looking to fortify their FusionTrust connectivity with multi factor level of authentication for different types of devices called Alpha FusionAuth.
After Implementing Zero Trust Connectivity, do you think you are done?
Not even close….
After integrating Alpha FusionTrust Connectivity based on Zscaler vendor or any other type of vendor.
- You also need to monitor the entire architecture, absolutely every single factor associated with the deployment of Alpha FusionTrust connectivity including multi factor authentication process, connectors, and entire enterprise for health of application connectivity and your users, which to be honest is not exactly straight forward or no where trivial endeavor.
- Luckily not all hopes is lost. Our company specializes in Enterprise Monitoring Solutions helping your critical infrastructure get monitored.
- As part of our Alpha FusionSmart solution offering we also can help companies visualize their entire environment in tools like New Relic,DataDog, LogicMonitor, SumoLogic, AppDynamics, Zenoss or Splunk, Solar Winds or even in a unified portal called Alpha FusionView For more info visit our monitoring services.
With Alpha FusionAuto Solution
- With the help of our Alpha team we can help companies, reduce manual repetitive tasks into automatic BOT transactions, running on scheduled basis helping your staff focus on what’s more important vs repetitive tasks.
- As we create these automated transactions, depending on what ecosystem we are dealing with appropriate languages and frameworks will be used.
- Where each of these frameworks will be executed by our our central management system that consists of multiple automation tools, what is commonly referred to as Alpha FusionAuto Tool Kit.
- Tool kit is holistically designed to help with automating manual transaction.
- Imagine the amount of hours your company can save, simply by identifying repetitive tasks and automating them. Think of how much money your organization can save.
- As part of our Alpha FusionAuto Enterprise Management service, our Alpha team can help you identify such repetitive transactions.
- With the help of our Business Analysts and Data Analysts experts we can visualize the frequency of manual events and convert them into automated processes, all that while working with your existing staff subject matter experts.
- Once automated transactions are executed, they need to be maintained throughout the entire lifecycle of the process.
- That means visualizing the lifecycle in either your existing automation tools that perhaps your company already invested in or in your SIEM.
- Or alternatively visualizing your automated transactions directly in our custom created data analytics SaaS tool Alpha FusionView, that can directly interface with our very own Alpha FusionAuto Tool Kit.
- Regardless which tool you chose to have it visualized in, whether it is your own or our tool, our Alpha team can help you visualize these transactions.
- Not only can we visualize the actual logic from the beginning to end of the transaction, but we can literally show entire data chain including origination and finalization of transaction.
- Often many of our customers already have existing tools, and do not want to spend any money on any other automation tools. Instead many customers seeking to utilize their automation tools to the best of their abilities.
- Luckily as part of our Alpha FusionAuto Enterprise Managed Services, we can help companies managed their existing tools utilizing best practices while helping companies save money.
- We have dedicated experts for specific tools already in house that can be instantly utilized for your automation needs.
- For any experts that we don’t have in house, we have entire Alpha Recruitment division for on boarding new Alpha team members for any specific automation tools.
- After transaction is executed, and everything goes well, there maybe nothing to look for, however what if your transaction does not get automated all the way?
- What happens if it doesn’t make it’s way through entire data chain?
- How will you know where it failed during which intermediate path?
- Where did it fail in the data chain?
- Luckily with our Alpha FusionML solution we can visualize entire distributed path of your automated transaction, ranging from showing exactly where the transaction started, where it ended, show it all visually in the geo based 3d map, show you which application ran the transaction, where the application is hosted, what micro-service initiated the transaction and what proxy or API gateway passed the transaction.
- Or Alpha FusionML tool kit is all about machine learning, data chaining, anomaly detection and forecasting and integrates directly with our Alpha FusionAuto Tool Kit.
- Let’s say we did create automatic BOTs in your environment to track different types of workflows.
- Let’s say we visualized results of these bots in our Alpha FusionAuto Tool Kit.
- But wouldn’t it be nice to know how normal your automatic bot execution is?
- What is considered normal and what is not?
- When BOTs for example fail to execute?
- Or When BOTs execute, but it takes longer…
- Or what happens if there is some other external factor associated with the BOT execution, but not directly related to it, yet needs to be considered as part of anomaly?
- All of these are valid questions, and that is precisely why we created Alpha FusionML solution to address anomaly related questions as it pertains to any type of data anomalies, regardless if it’s coming from BOTs or combination of different factors as it pertains to automatic execution of BOTS and some other environmental enterprise factors.
- With Alpha FusionML solution not only can we visualize how BOTS behave….but we can stitch the data together originated from the results of the BOTS execution to the results of the application health status… and build anomaly score based on that directly as part of our Alpha FusionML solution.
- We can feed data results directly from Alpha FusionAuto Tool Kit into Alpha FusionML software in order to provide valuable insights for what is considered to be anomalous behavior and what is not.
- Plus based on the data we obtain from combinations of BOT running automated processes, application health and your infrastructure environment results we can craft custom machine learning models as part of our Alpha FusionML solution to create forecasted visualizations and alerting, taking you BOT automation processes one step further.
With so many imaginative points you do not have to imagine anymore.
- Instead let us explain precisely what our Alpha FusionAuto solution has to offer.
- Over the years we have developed experience and created our very own frameworks for automating critical transactions,
ranging from users accessing applications, machines executing sensitive system processes, to software testing. - And now we are consolidating our discoveries into Alpha FusionAuto solution.
That consists of a managed service, and your very own tool kit. - Our managed service helps customers automate their existing environment,
using tools customer already owns,
while filling in the blanks with our very own Alpha FusionAuto Tool Kit. - With Alpha FusionAuto Tool Kit, we can build and deploy BOT automated processes across hybrid or multi cloud environment
regardless of what type of language or infrastructure your company is running on. - Additionally with Alpha FusionAuto tool kit, we can directly integrate
with your existing automation software, such as UI-Path, Control-M, Ranorex, Mulesoft and others. - The best part about Alpha FusionAuto solution is that we don’t just integrate with your existing automation tools,
but we also help you manage and maintain your software as part of our Alpha FusionAuto Enterprise Managed Services. - Which means we work with your existing echo system of automation software, helping you to ensure your tools
run smoothly and accurately. After all automation tools needs to be maintained, BOT activities need to be babysat,
you can’t just deploy and forget automation bots, that would be risky and costly. - With Alpha FusionAuto Enterprise Managed Services, your company gets the benefit of having,
dedicated team of Alpha experts working side by side together with your staff in creating, deploying and maintaining BOTS,
helping you reduce risk, and save on costs by utilizing best practices. - Additionally our Alpha FusionAuto tool kit can be integrated with our other flagship solutions,
ranging from anomaly detection, machine learning, data chaining, forecasting, data unification,
cyber security, & zero trust networking. - To Learn More About our Solution Offering Contact us
and let us know your use case, to see how we can help you,
with your automation needs.
In Summary
- Our company can create customized automation solution offering just for your specific enterprise need.
- Reach out to us, let us know your use case, we can get together analyze what you have, and provide your recommendation on how to move forward with what tool, what to automate, how to automate and monitor critical KPIs.
- We can also provide you presentation for some of the services that we did for our other customers in the field of Machine Learning, Certificate LifeCycle Management, Network Monitoring and beyond.
- If interested send an email to [email protected] or send us a message from the chat icon or fill out the form or call us, and simply let us know your use case.
- Thank You for taking your time to read about our Alpha FusionAuto Solution.
Industries We Service
Travel and Aviation
Consulting
We help companies monitor Airport Networks and ATM devices, as well as wireless access points.
Financial Services
Consulting
Our company helps Loan Processing firms, Banks, and other financial institutions monitor combination of both on premise and in cloud resources.
Education
With Entuity we can monitor Campus networks for real time changes on infrastructure such as firewalls, routers, switches, SDN controllers.
Law Firms
We also work close with Law Firms and other types of legal organizations seeking to monitor their cloud and on premise resources.
Manufacturing
Our company can help customers add foam spray pumps, or any other types of manufacturing devices, or IoT devices into Entuity monitoring software.
Accounting and CPA firms
Our company helps CPA accounting firms monitor their network for newly discovered devices, and changes in data.
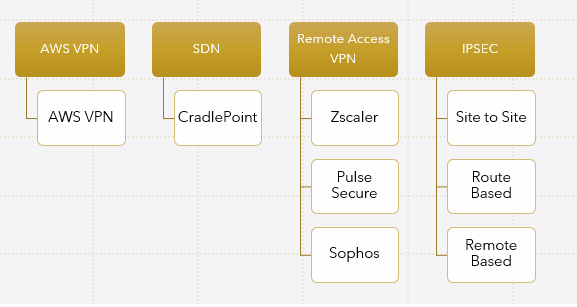
Alternative Connectivity Solutions that we can work with
We can help customers with their UTM and Sophos XG or other firewall models get connected to AWS cloud.
We can work with Cradlepoint IBR routers and other types of cellular routers to help you create SDN solution with direct access to the cloud over OpenTLS.
We can help your company have secondary level of remote IPSEC access directly to Pulse Secure Appliances installed in the form of AMI in AWS cloud.
We can help customers get integrated with Zscaler as primary method of communication for remote access VPN, with combination of some other vendor like Pulse Secure in AWS as secondary vendor.
We can help customers create VPN tunnels through transit gateways to CSRs hosted in AWS cloud from the remote branches and we can help run EIGRP over DMVPN tunnels or even OSPF.
We can work with GAIA R77 and up version appliances helping customers get connected to the cloud in either routed or policy based routing way.
We can help customers with Cisco ASA connectivity to AWS cloud, using active and standby type of fail over methods.
We can help with Edgerouter connectivity from behind the NAT devices.
We also work with customers who have FortiNET environment and seeking help to interconnect their on premise networks to AWS cloud either through built in native features of AWS using virtual private gateways or to Fortigate Appliances in AWS cloud.
Problems and FusionTrust Solutions
Maintaining VPN tunnels is complex, although understandable in a complex multi cloud environment. Instead FusionTrust connectivity can be used, where your company would rely up on Zero Trust Architecture for inter-connecting your networks, and our company can help you integrate such architecture, either with Zscaler or another type of vendor, whomever is most affordable for your organization’s budget.
Our company can help you dissect cost factors and evaluate multiple vendors for your connectivity needs, including the vendors that you may already be engaged with, providing that they are based on Zero Trust Architecture. (if not than we offer separate consulting connectivity service offering for such cases)
Indeed, not every application is compatible with proxy. However our consultants can assist with deciphering your existing applications, to see if they could be made compatible with Zscaler Proxy. Either through the process of bypassing it, or application re-architecture, or modification of connectivity architecture through alternative means of connectivity beyond Zscaler such as your secondary VPN solution provider working in parallel with primary FusionTrust connectivity solution.
- Luckily there is no CA associated with Zscaler, Zscaler acts like a CA, when it comes to generating keys and associating them with Zscaler connectors.
- However, that doesn’t mean that you should just forget about certificate management.
- There is still certificate lifecycle management concept being involved just like with every thing else.
- Last thing you want to do is forget about renewing your cert.
- Our CLM and PKI solutions can help your company fortify your FusionTrust connectivity by ensuring that the certificate lifecycle is being managed and not forgotten. and certs are renewed regardless if it’s for individual connectors or for SAML based authentication or any other types of infrastructure that may exist in your enterprise beyond Zscaler. To learn more about our CLM and PKI solution offering visit this link.
- Indeed when it comes to FusionTrust connectivity there are other factors that can exist in your environment that may bock such connectivity such as NACLs or inbound or outbound security groups.
- Not to mention other factors that may exist in your environment, ranging from CrowdStrike agents on laptops, to Zone Based Firewalls on the routers, and Intrusion Detection or IPS types of connectivity restrictions configured on customer’s firewalls.
- Managing and seeing all of these connectivity restrictions is the key, after all FusionTrust connectivity relies on the underlining connectivity sort of like BGP relies on already pre-established connectivity prior to being connected on port 179 over TCP.
- Luckily our company can help companies visualize connections that are getting blocked across entire layer 1 through 7 stack through what so called FusionView unified portal, visualizing multiple types connectivity restrictions across your entire enterprise.
- Together with FusionTrust and FusionView the process of identifying what is being blocked where, becomes extremely simplified.
- Alternatively our company can help customers integrate many of the security systems that are responsible for blocking access with customer’s existing SIEM regardless if it’s Sumo Logic, Splunk, ELK stack or other.
Indeed any time application gets patched, it’s possible that after patching some new FQDN names get introduced or original URL where the application was hosted out of a sudden stops working, causing users not being able to connect to application.
- Luckily as part of our FusionPatch solution offering, our company verifies application health state after the patch is complete. Hence not only do we deploy patching solution architecture, we help you maintain it it’s health state.
- Our FusionView unified portal can help customers visualize application health state, before and after patch deployment.
- Our FusionTrust consultants can help your company reverse engineer application connectivity needs to see if it can be proxy compatible.
- In cases if the application is not proxy compatible, it can either be bypasssed or escalated to our App development team to help you customize architecture of the application that you are using in order to make it compatible.
Other Integration and IT Services Similar to FusionTrust service
-
AlphaCICE & Alpha FusionView Service Details
Read moreMinimize false positive, duplicate alerts with AlphaCICE central intelligence correlation engine. AlphaCICE and unify all of your tools AIOPS events in a single pane of glass with Alpha FusionView. See how Alpha FusionSmart Enterprise Monitoring service that Alpha Technologies offer ties it all up together in context of multiple ITIL best practices phases.
-
AlphaCICE – Central Intelligence Correlation Engine
Read moreMinimize false positive, duplicate alerts with AlphaCICE central intelligence correlation engine. AlphaCICE is a custom solution and service offered by Alpha Technologies that is specifically designed for financial industries seeking to take control of their incident management process. Incident Managers can maximize their operational effectiveness through streamlined operationalized workflows, by relying on correlated supervised and unsupervised AIOPS classified intelligence fetched from your already existing monitoring tools. AlphaCICE is explicitly designed to reduce multiple events into a single actionable event that matters most, by empowering data owner operators with prescriptive & AI & ML driven recommendations
-

Alpha Digital Transformation of Applications & Tech Stack
Read moreAlpha Digital Transformation solutions for all size businesses seeking to secure their legacy application in order to minimize risk, while in parallel migrate the application and tech stack into modern API invokable and event driven ecosystem helping data owners get closer to their data.
-

Alpha AWS | AVD | Office 365 Virtualization Solutions
Read moreAWS Desktop and Network Virtualization solutions and services for small, medium & large size companies seeking to solve high latency connectivity related problems, while maximizing security.
-

Alpha FusionChain Innovative Solution for BlockChain Database and Monitoring
Read moreMigrate Your Legacy applications to Blockchain faster and safer without disruption of the existing workflow. With our tool kit we can help companies build, deploy maintain and manage Blockchain architecture helping you revolutionize your microservices and decentralized architecture. We can build Blockchain networks for multiple use cases ranging from NFTs, Crypto, MetaVerse and beyond.
Other Solutions & Services that we offer
Why Customers Pick Us

Automation of Applications
Automation of monolithic and microservice types of applications, software testing and quality assurance. Helping companies minimize manual tasks in every day operations and reduce costs by leveraging custom built automation scripts for your enterprise infrastructure, ranging from automation of APIs to orchestration of complex resources.
Read More
Expertise in Cloud and On Premise Environments
Expertise in AI and ML with multiple clouds AWS, Azure, GCP, Kubernetes, Serverless Lambda Functions, Docker containers, and beyond as well as on-premise network & app infrastructure environments.
Read More
Unified View
Custom-built view bridging your micro-services and monolithic application, infrastructure, and monitoring need all in one portal. For example, ServiceNow, Jira, CMDB, BMC Control M and Microservices all in 1 portal, helping customers visualize, slice, and dissect data as well as create reports, trends, and forecasts, based on results of any data, either coming from your on-premise or in cloud environment
Read More
Based on Zero Trust Connectivity Architecture
Get your on site locations and remote office work force or IoT devices connected with the help of custom solutions designed to keep companies secure, while protecting employees form malicious threats.
Read More
FusionCLM PKI Solutions
Certificate Lifecycle Management (CLM) and PKI services and solutions for companies seeking to take control of their certificate validation and enrollment needs, helping companies reduce risk
Read More