Microservices Monitoring
Serverless Lambda Function Monitoring, Kubernetes Clusters, & Monolithic Applications.
Solutions for Microservices Monitoring Applications
Whether you are in the process of monitoring monolithic applications or microservices, the need for full level observability never ends. With the advances of microservices and server-less architecture, the complexity of being able to monitor infrastructure has increased substantially. Solving a problem in the world of microservices architecture is like trying to solve a murder mystery.
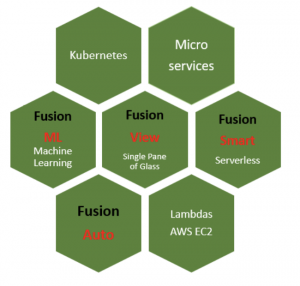
- Which is precisely the reason why our company DBA Binary Fusion created a brand new service specifically to handle the hassle of monitoring Microservices and server-less architecture. Introducing Fusion View, custom solution designed to help companies gain full visibility of their entire Layer 1 through Layer 7 application stack.
- Ranging from network environment, infrastructure level monitoring, where we can help you monitor Kubernetes clusters, to microservices applications as well as Lambda functions all in a single pane of glass style of centralized view called Fusion View.
Or Fusion View single pane of glass dashboard is designed around customer's environment.
Some of the use cases that we can help with
Web E-Commerce Monitoring for Financial Client Industry
- For example some customers would like to monitor their e-commerce web-store that contains everything ranging from front end services to back end services, residing across different clouds (AWS, Google, Azure) different regions and ec2 instances, where multiple lambda functions are executed left and right, to auto-scaling ec2 instance where ec2 instances get terminated and turn back on dynamically, resulting in frequent state of change.
- Other customers would like to monitor everything mentioned above, plus availability of their application based on multiple key performance indicators ranging from ping latency, authentication error count, number of 404 error codes, disk space utilization, multi factor authentication requests, and everything in between that is responsible for availability service, pulled together into singular unified health score tied to the machine learning prediction mechanism, helping customers not only identify when availability is impacted the most, but also be able to see when it will most likely be impacted ahead of time.
Our company DBA Binary Fusion understands the need and importance of being able to monitor complex architecture. We have architected many of our own websites, applications and other types of solutions, ranging from search engines to complex micro-services based applications that are responsible for critical business transactions and we understand the importance of making sure that the transaction monitoring is the key in reducing mean time to resolution and identification of the problem.
What we have discovered during creation of FusionView
- As we continued to evolve our Fusion View solution we realized that many companies have few things in common, and these few things in common happens to be being be: being able to reduce alert noise, being able to visualize the overall complexity of solution architecture into a simple glass table that displays the overall health state of entire application stack across layer 1 to 7.
Monitoring Full Stack Layer 1 through 7 is not so easy anymore
- Monitoring Layer 1 through 7 using traditional monitoring solutions when it comes to dynamic nature of micro-services is no longer the wise thing to do. Traditional SNMP based monitoring and APM tools are quickly falling out of favor for many of the customers. What used to be an easy way of monitoring applications out of sudden became not so-easy.
- With the evolution of dynamically scaled ec2-instances, and pods spinning up left and right jumping from one of the Kubernetes nodes to another within the cluster, identifying the issue becomes harder than it was ever before, in comparison to monolithic style of applications.
Why is not Easy?
Ephemeral Data causes complexity
- Customers when it comes to monitoring KPIs not only want to monitor them, but want to also predict when certain KPIs will end up causing problems. Machine learning algorithms don’t exactly keep up with the speed of the rapidly moving KPIs. Problems happen fast, and sometimes go away just as fast, without leaving traces behind. The ephemeral data causes huge cardinality causing traditional monitoring tools not being able to keep up.
Customer environments are split in Silos
- Many customers have different teams within their environment working in Silos, yet microservices and server-less based application require unification of expertise across multiple teams, something that many customers are not exactly used to.
Multiple IT expertise are required
- Being able to monitor entire stack requires inter-combination of different types of expertise such as, cloud engineering expertise, networking, security, business KPIs identifications, SREs, data scientists, data engineers, automation engineers, monitoring tools subject matter experts and beyond.
Large amount of time is needed to understand and monitor microservices
- Even if customers already have all of the resources who perhaps can create something like single pane of glass view, it is no secret that the centralization and identification of every single KPI and realization of data flow and underlining level of architecture can eat insane amount of time, and even if customer succeeds in creating such level of monitoring, they must be able to maintain it and monitor the monitors. (something that many customers simply don’t have the in house expertise in).
Research and development is required
- Customers who do decide to take upon this incredible single pane of glass observability journey to monitor their existing lambda functions, as well as micro services running across different pods, and all the other underlining components will without a question face many challenges that will require insane amount of research and development. (something that many customers simply don’t have time for).
Monitoring Microservices requires visibility not just into metrics data, but also logs
- Many customers are not entirely sure how to monitor their applications beyond relying on metric data, yet the reality of it all is that microservices based monitoring requires beyond looking at metric data and involves looking at logs. (Customers are not exactly excited about looking at logs, after all it requires advanced level of expertise, being able to parse them and decipher them).
ITSM and CMDB integration becomes a necessity
- Many customers have already existing CMDB and ITSM systems that behave as single source of truth, yet not exactly sure how to integrate CMDB systems with real time monitoring. (After all integrating CMDB and ITSM systems such as Service Now is not exactly walk in the park, requiring eccentric integration expertise that many customers simply lack).
Cost Reduction and Performance juggling can be a challenge
- Monitoring micro-services architecture requires visualizing different types of data sources, keeping up with the data ingestion, while juggling between performance, security and cost reductions. (not exactly easy to achieve without advanced search querying expertise, data identification, partitioning, pre-processing and data ingestion best practices know how expertise.)
Long term data retention for trend patterns and real time visualization requires advance integrations
- Many customers want to have long term data retention monitoring and also as close to real time data monitoring as possible. (easier said than done, real time data visualizations require advanced level of Kafka, MangoDB integration with the monitoring solution something that is not exactly easy to build without understanding the whole scope of the development effort)
Some monitoring processes require the use of Automation
- Many times business transactions require custom automation jobs designed for example to stream continuous data. For example let’s say .CSV file needs to be modified, in order for monitoring tool to detect time series based data it would require generating continuous update within the file for change to take place, something that will require automation. (not every customer likes to poke around APIs, wondering and pondering for how to generate automatic process).
Correlating data from micro-services that are changing it's state dynamically is not so easy
- Many times customers require deep level of correlation between the data, and working with their existing teams to identify what matters the most prior to visualizing the data. (This task alone requires stitching correlated entities that matter together, and talking to multiple teams such as enterprise team, networking, infrastructure, operations, security, business, and beyond)
Learning concepts of micro-services just so you can monitor your applications can be difficult
- Many customers who do end up visualizing specific set of applications or solutions, often can not carry over the knowledge transfer to the rest of the team, and the monitoring tool often becomes abandoned or barely used.
After micro services and lambda functions are monitored the path to remediation is not exactly a walk in the park
- Many customers don’t just want to monitor their environment, but also would like to have either automated or semi-automated resolution to the underlining problem. (This is not exactly easy to do without, having expertise in data automation, remediation and realization that something went wrong).
Keeping up with compliance monitoring requirements in the world of dynamic changes is not easy
- Many customers have different types of compliance requirements and require masking of sensitive information such as social security numbers prior to data getting into the monitoring tools. (such masking needs to be done prior to showing data within the visualization tool, in order to reduce risk of sensitive data being shown in front of unintended eyes, something that requires specialized set of expertise )
Solving a problem in Serverless Environment is like trying to solve a murder mystery.
Well...

Problem
Monitoring non monolithic applications is complex.
When it comes to monitoring monolithic applications for CPU, Memory and other information it’s a lot easier to do vs trying to monitor services in micro services based architecture, where at any given time service may or may not exist.
Many services now days are scatters across different types of containers, residing across multiple PODs, where at any given time POD can be terminated and respawned on the fly.
The typical question that resides is how do you monitor thousands of containers that constantly come and go.
Typical monolithic monitoring tools can’t deal with high level of cardinality and ephemeral data?
The answer is for every problem there is a solution
Depending on what type of device is trying to authenticate with the network, the authentication capabilities may vary. For example, some may support certificates, while others may support no such thing, but perhaps have some process or a service, or a registry key that is running in Windows OS for example.
IoT devices may have unique processes/services that can be tracked for validation.
Yet the problem is it’s hard to monitor devices that constantly come and go.
Imagine monitoring not just devices, but lambda functions and auto-scaling ec2 instances… that’s when the real fun begins.
Yet with every unique problem, there is a unique solution.
DBA Binary Fusion can help you tackle these Identity Validation problems with unique solutions.

Solution
So how do you validate different types of devices and applications if certificates can not exactly be deployed?
The answer is to use multiple layers of validation.
- For example if your environment consists of laptops that have operating systems such as Windows and MAC OS, then there are multiple validation tools that exist out there that makes the concept of recognizing that the the laptop is company’s laptop and not just some rogue device.
- Yet the reality is that many of the tools on the market require sophisticated level of understanding about all the eccentric functionalities.
- Many of the tools on the market makes concept of realizing what works or what doesn’t difficult to decipher.
- Managed windows devices maybe easier to handle with Enterprise application tools such as Microsoft Endpoint Manager (formerly known as in-tune), while MAC devices are easier to handle with tools like JAMF and Apple Business Manager.
- Yet what about other devices such as the ones that do not have certificate validation capabilities or enterprise MDM system to handle the requests, how can such types of devices be handled from validation standpoint?
Introducing Microservices Monitoring Solutions
Imagine
-
- Being able to monitor your entire application stack based on multiple views ranging from Executive, Operational, Technical perspective and beyond.
- Being able to monitor micro-services, lambda functions, or any other dynamic state of change entities at almost real time, in combination of gaining benefits from machine learning prediction algorithms and in combination of being able to visualize business transactions without over-investing into research and development, without having to worry about having multiple in house teams to achieve such level of full stack monitoring, without having to worry about learning underlining queries and monitoring tools, without having to recruit any body for helping you monitor your application.
- Being able to visualize your application even if it runs across multiple clouds, different regions, virtual environments, Kubernetes clusters, on premise infrastructures and beyond.
- Being able to monitor not only CPU and memory of let’s say every node within the Kubernetes cluster, but also be able to monitor underlining applications. Whether these applications are running on different pods, or on ec2 instances or AIX environment. Whether these applications are home brewed or vendor based.
- Being able to monitor not only what’s happening within the environment from the destination perspective, but also be able to monitor source client interconnectivity to your application from multiple geographic regions, using inter-combination of bots and distributed tracing.
- Being able to monitor not only what’s happening in the cloud, but what happens even before packet gets to cloud and traverses through your physical infrastructure such as routers, firewalls, switches and load balancers.
- Being able to monitor your existing applications not only from metric stand point, but from logs as well.
- Being able to visualize multiple business transactions in a single view, using inter combination of dynamic templates and custom built search queries specifically designed to help customers visualize multiple business services in a single view without having to jump across too many views.
- Being able to reduce costs on data ingestions with the Binary Fusion customized best practices framework, where we can help you either eradicate data ingestion costs all together by crafting up custom built in house micro-services based monitoring development solution or we can alternatively work with your already existing monitoring SIEM tools helping you gain control of your environment and reduce costs.
- Being able to have as close to real time visualization of business KPIs as much as possible. Our custom integration solutions ranging from Kafka to MangoDB integration with your existing monitoring tools or custom built tools will help you see data close to real time as much as possible.
- Being able to work with what you got, meaning if you have already invested into existing monitoring tools where contracts still present, there is no reason why you should just abandon them, our company have created strategic partnership working with multiple monitoring tools helping customers work with what they got while gradually exploring other options that can help them reduce costs.
- Being able to have your micro services based applications automated in order to achieve correct level of monitoring and visibility without having to dig around complex REST APIs. Our company can help with API Discovery, process automation and beyond.
- Being able to rely on one team with already developed data visualization and analytics expertise, that can help you build single pane of glass dashboards, business transaction analyzer views as well as train your existing IT and business teams in how to use the dashboard without spending your time on having to provide such knowledge transfer.
- Being able to not only identify what’s wrong from the eagle eye view Tony Stark style of visualized FusionView perspective, but also being able to benefit from process automation, identification and remediation as a service commonly referred as RAAS.
How exactly does FusionView works?
The way it works is we wrap our micro-services monitoring solutions around customer’s existing monitoring tools, cost reduction initiatives and needs.
- We can help your company monitor micro services and lambda functions as well as monolithic applications and entire infrastructure and unify it all in a single pane of glass.
- We work together with different types of customers ranging from multiple industries such as Finance, Banks, Loan Processing Agencies, Professional LLCs, Manufacturing companies, Law Firms, accounting firms, insurance companies, health sector and others.
- We custom craft monitoring solutions in the based on the customer’s needs.
- We maintain the monitoring environment and work with your existing stake holders and teams to create custom visualizations as well as helping your teams onboard data while following best practices to reduce data ingestion costs.
- We provide knowledge transfer to your existing team, helping your in house teams begin using the dashboards and increasing the greater rate of monitoring tool adoption which ultimately reduces risk.
- We create correlation queries within searches to help you visualize relevant KPIs in the same place.
- We utilize your existing SIEM wherever possible and work with other in house tools to bring them into single pane of glass.
- We can create custom playbooks for your existing Business Operations team and other teams helping them better understand what to do when monitoring event occurs.
- We can work with your existing ITSI and ITSM system helping you visualize your microservices data in a way that will help customers reduce their time to resolution.
Other Services We Offer
In addition to offering multi factor level of validation across either certificates or other validation characteristics also being able to visualize your entire environment in tools like New Relic,DataDog, LogicMonitor, SumoLogic, AppDynamics, Zenoss or Splunk, Solar Winds.
This service is specifically designed around AI and machine learning, data preprocessing, feature engineering, model selection and training, using supervised and unsupervised data sets.
This service is specifically designed around micro services and server-less based monitoring, that means instrumenting agents into your existing application stacks, in order to ensure that your micro services based applications end up showing up in tools. Onboarding your micro-services data gathered into monitoring tools. Analyzing APIs from multiple data sources, and creating necessary integrations revolved around real time monitoring, CMDB and ITSM integrations.
This service is designed around automation, meaning creating necessary automation processes that are designed to help your data become ingested automatically. During this service is where we create BOT processes utilizing different types of automation tools, ranging from Python Scripts, to Terraform, Chef, Puppet, Ansible and others.
Remediation as a Service solution by Binary Fusion
Many of the customers require some semi-automatic or automatic methods that can help them resolve problems. Our company can help bridge the gap between automation, visualization and remediation in one service, where all 4 services Fusion services come together with the common goal of helping customers discover when something breaks and fix it automatically, or semi-automatically when it is broken. To learn more about any of our services don’t hesitate to contact us for a customize presentation specifically designed for you.
If interested in our microservices monitoring solution, then don’t hesitate to fill out this form.
Applications we can monitor
We can help customers monitor applications running in Kubernetes clusters from both infrastructure standpoint for traffic between pods, containers, and applications within the containers.
We can help customers monitor serverless lambda functions.
We can help customers monitor on premise or in cloud monolithic applications.
We can help monitor server and client based applications running on Windows or Macintosh devices.
Microservices applications running on IoT types of devices, Raspberry Pi, Arduino, and many others..
Problems and Microservices Solutions
Monitoring pieces of application code or infrastructure, with high level of cardinality can be challenging using traditional monitoring tools. We have developed unique frameworks and specialized tools making it easy to monitor microservices types of architectures.
Microservices running on Kubernetes clusters within Docker containers are not the only pieces that need to be monitored. Applications running inside of the containers, need to be monitored as well. We have created a framework that makes it easy to monitor microservices applications, using logs, distributed traces and metrics.
Exporting data metrics from microservices based applications for ML and AI analysis is not the most trivial task in the book. As part of our FusionML Machine Learning services. Our in house experts, can help with building AI and ML models based on microservices data output for your specific type of use case.
Finding a problem in the world of microservices architecture is like solving a murder mystery. Our experts can help you overcome this hurdle. We have created troubleshooting workbooks designed just for that.
Microservices can be in AWS cloud, east or west region, on premise, Azure or anywhere else.
We have created unique data visualization tool FusionView that makes it easy to see where your microservices are running at.
Vulnerabilities and exploits exist not just in monolithic applications, but in microservice types of applications as well. Solving these vulnerabilities is not exactly a walk in the park. We have customized FusionPatch and Fusion Scan solution helping customers with identifying vulnerabilities as well as patching them.
Automating applications that are running as microservices requires specialized skillset, not only in programming automation languages, but in understanding of the actual application itself.
With the help of FusionAuto framework we can help customers automate their micro-service based applications.
In Summary
- Reach out to us, let us know your use case, we can get together analyze what you have, and provide your recommendation on how to move forward with what tool, what to monitor, how to monitor it and can also provide you presentation for some of the services that we did for our other customers in the field of Machine Learning, Monolithic Server Monitoring, Certificate LifeCycle Management, Network Monitoring and beyond.
- If interested send an email to [email protected] and simply let us know your name, company name, phone number, and what you are looking for, or alternatively contact us by the phone number shown on the top right corner of this website.
- Thank You for taking your time to read about our Microservices Monitoring Solutions Integration services.
Industries We Service and help customers integrate Multi Factor Solutions
Travel and Aviation
Consulting
We help companies monitor Airport Networks and ATM devices, as well as wireless access points.
Financial Services
Consulting
Our company helps Loan Processing firms, Banks, and other financial institutions monitor combination of both on premise and in cloud resources.
Education
With Entuity we can monitor Campus networks for real time changes on infrastructure such as firewalls, routers, switches, SDN controllers.
Law Firms
We also work close with Law Firms and other types of legal organizations seeking to monitor their cloud and on premise resources.
Manufacturing
Our company can help customers add foam spray pumps, or any other types of manufacturing devices, or IoT devices into Entuity monitoring software.
Accounting and CPA firms
Our company helps CPA accounting firms monitor their network for newly discovered devices, and changes in data.
Other Integration and IT Services Similar to Multi Factor Validation services that we offer
-
AlphaCICE & Alpha FusionView Service Details
Read moreMinimize false positive, duplicate alerts with AlphaCICE central intelligence correlation engine. AlphaCICE and unify all of your tools AIOPS events in a single pane of glass with Alpha FusionView. See how Alpha FusionSmart Enterprise Monitoring service that Alpha Technologies offer ties it all up together in context of multiple ITIL best practices phases.
-
AlphaCICE – Central Intelligence Correlation Engine
Read moreMinimize false positive, duplicate alerts with AlphaCICE central intelligence correlation engine. AlphaCICE is a custom solution and service offered by Alpha Technologies that is specifically designed for financial industries seeking to take control of their incident management process. Incident Managers can maximize their operational effectiveness through streamlined operationalized workflows, by relying on correlated supervised and unsupervised AIOPS classified intelligence fetched from your already existing monitoring tools. AlphaCICE is explicitly designed to reduce multiple events into a single actionable event that matters most, by empowering data owner operators with prescriptive & AI & ML driven recommendations
-

Alpha Digital Transformation of Applications & Tech Stack
Read moreAlpha Digital Transformation solutions for all size businesses seeking to secure their legacy application in order to minimize risk, while in parallel migrate the application and tech stack into modern API invokable and event driven ecosystem helping data owners get closer to their data.
-

Alpha AWS | AVD | Office 365 Virtualization Solutions
Read moreAWS Desktop and Network Virtualization solutions and services for small, medium & large size companies seeking to solve high latency connectivity related problems, while maximizing security.
-

Alpha FusionChain Innovative Solution for BlockChain Database and Monitoring
Read moreMigrate Your Legacy applications to Blockchain faster and safer without disruption of the existing workflow. With our tool kit we can help companies build, deploy maintain and manage Blockchain architecture helping you revolutionize your microservices and decentralized architecture. We can build Blockchain networks for multiple use cases ranging from NFTs, Crypto, MetaVerse and beyond.
Why Customers Pick Us

Automation of Applications
Automation of monolithic and microservice types of applications, software testing and quality assurance. Helping companies minimize manual tasks in every day operations and reduce costs by leveraging custom built automation scripts for your enterprise infrastructure, ranging from automation of APIs to orchestration of complex resources.
Read More
Expertise in Cloud and On Premise Environments
Expertise in AI and ML with multiple clouds AWS, Azure, GCP, Kubernetes, Serverless Lambda Functions, Docker containers, and beyond as well as on-premise network & app infrastructure environments.
Read More
Unified View
Custom-built view bridging your micro-services and monolithic application, infrastructure, and monitoring need all in one portal. For example, ServiceNow, Jira, CMDB, BMC Control M and Microservices all in 1 portal, helping customers visualize, slice, and dissect data as well as create reports, trends, and forecasts, based on results of any data, either coming from your on-premise or in cloud environment
Read More
Based on Zero Trust Connectivity Architecture
Get your on site locations and remote office work force or IoT devices connected with the help of custom solutions designed to keep companies secure, while protecting employees form malicious threats.
Read More
Based on Zero Trust Connectivity Architecture
Certificate Lifecycle Management (CLM) and PKI services and solutions for companies seeking to take control of their certificate validation and enrollment needs, helping companies reduce risk
Read More